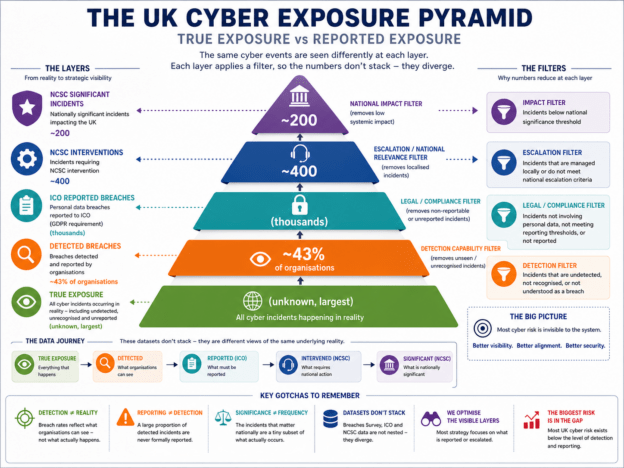
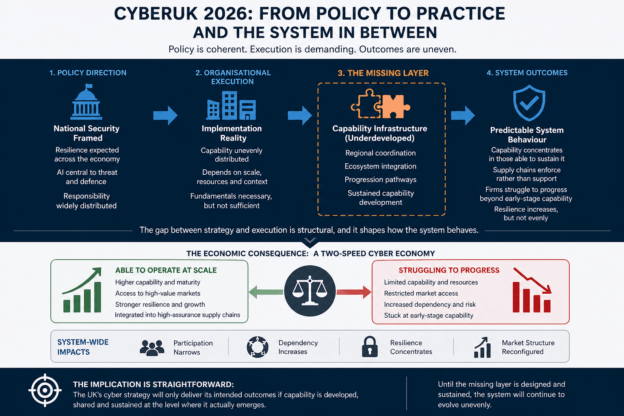
The 2026 DSIT Cyber Security Sectoral Analysis reveals more than continued growth in the UK cyber sector. Beneath the headline statistics sits a deeper structural transition: cyber is increasingly becoming a distributed economic infrastructure tied to industrial resilience, operational continuity and supply-chain assurance. This article examines the implications of regionalisation, slowing employment growth, rising productivity pressure and AI-driven dependency complexity, particularly for industrial regions such as the West Midlands.
Continue reading