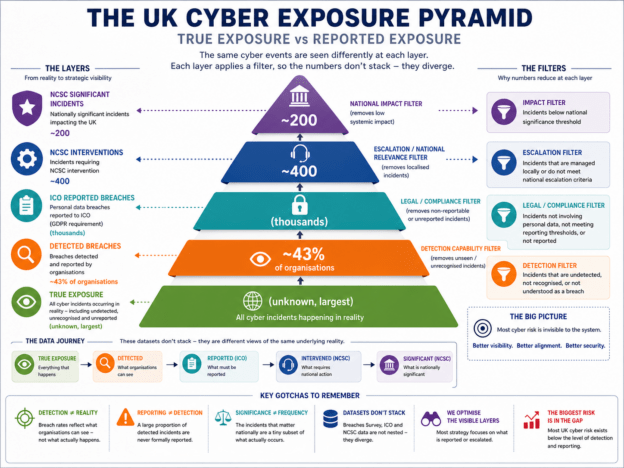
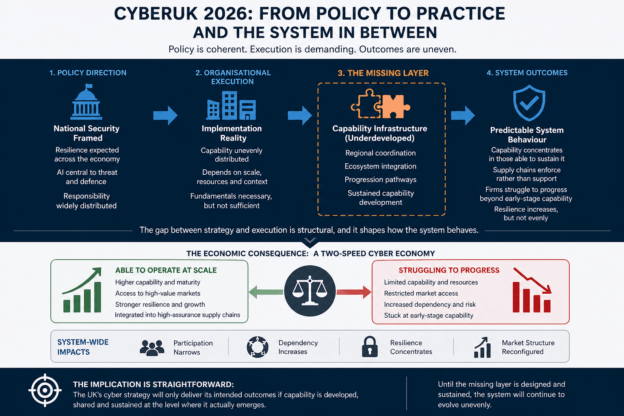
The UK’s cyber security data does not describe a single reality; it describes three filtered views of it. By overlaying Breaches Survey, ICO, and NCSC data, a clearer model emerges: one of layered visibility, not layered severity. This article introduces a “true exposure vs reported exposure” framework, showing that most cyber risk sits below what is detected, reported, or acted on, and that the current strategy is focused on the wrong layer.
Continue reading