The UK Cyber Security Breaches Survey 2025/26 suggests stability, but closer analysis reveals a system stuck in place rather than improving. Breaches remain widespread, detection uneven, and incentives misaligned. What looks like progress is often an artefact of measurement. This article argues the UK has reached a cybersecurity plateau, where risk is normalised, resilience is incomplete, and meaningful change will require structural, not incremental, intervention.
Executive Summary
At first reading, the Cyber Security Breaches Survey 2025/26 feels familiar, almost reassuring. The numbers haven’t spiked. Some have even improved. It’s easy to conclude that, collectively, we’re getting better at cyber security.
That conclusion would be a mistake.
Look more closely, and a different pattern emerges: not improvement, but stabilisation at a level of persistent, systemic exposure. Nearly half of UK businesses still experience breaches annually. Larger organisations fare worse, not necessarily because they are weaker, but because they are more exposed and more aware.
More concerning is that some of the apparent improvement is likely measurement drift, not risk reduction. If fewer organisations recognise phishing, breach rates fall on paper while reality remains unchanged or worsens.
Across the dataset, a set of structural “gotchas” becomes clear:
- Cyber risk is now baseline, not exceptional: breaches are part of normal operations
- “Improvement” may reflect reduced detection, not reduced attacks
- Size correlates with exposure, not necessarily security maturity
- The dominant attack methods haven’t meaningfully changed in decades
- Governance is rising faster than operational capability
- Organisations underinvest because the economics still don’t work
- AI is accelerating existing problems, not creating new ones
Taken together, these are not signs of a system getting better. They are signs of a system that has adapted just enough to cope, but not enough to improve.
The implication is uncomfortable but important: the UK is no longer in a phase of rapid cyber security evolution. It is in a phase of managed stagnation.
And breaking out of that plateau will require changing incentives, not just raising awareness.
Contents
- Executive Summary
- Contents
- 1. Introduction
- 2. The Headline Numbers Hide the Real Signal
- 3. The “Improvement” is Statistical, Not Structural
- 4. Sectoral Reality: Size Matters More Than Capability
- 5. The Attack Landscape Hasn’t Changed (Much)
- 6. Governance is Improving… Slowly (and Too Late)
- 7. The Economic Reality: Cyber is Still Undervalued
- 8. AI is Not the Disruption: It’s an Amplifier
- 9. The Sectoral Insight: Cyber is a System, Not a Capability
- 10. What This Means for the UK Cyber Ecosystem
- 10.4 The Policy Response
- 11. Conclusion: A Plateau, Not Progress
- 12. Closing Thought for the Series
1. Introduction
The UK Government’s Cyber Security Breaches Survey 2025/26 is, on the surface, reassuring. Breach prevalence hasn’t surged dramatically. Some metrics have even improved slightly.
But read it properly, and in context, and a very different story emerges.
This is not a story of improvement.
It’s a story of structural stagnation at scale.
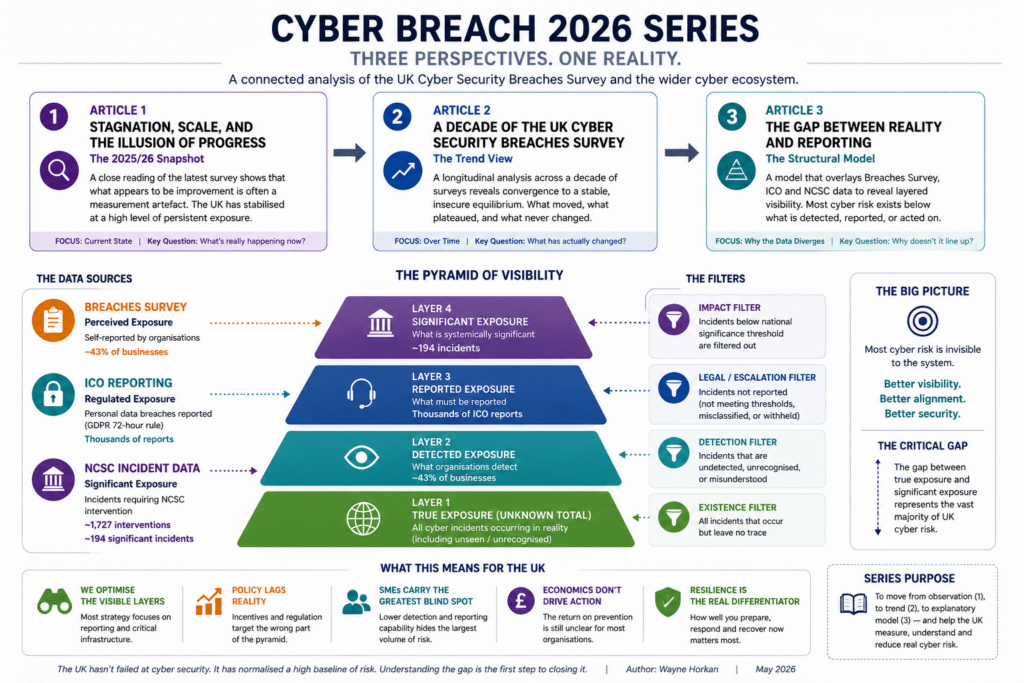
1.1 The Cyber Breach Series 2026
This article forms part of the Cyber Breach 2026 Series, a three-part analysis of the UK Cyber Security Breaches Survey and its wider implications for the UK cyber ecosystem.
Each article approaches the same dataset from a different angle:
- Article 1: Stagnation, Scale, and the Illusion of Progress
A close reading of the 2025/26 survey shows that what appears to be an improvement is, in many cases, a measurement artefact, revealing a system that has stabilised at a high level of persistent exposure. - Article 2: A Decade of the UK Cyber Security Breaches Survey
A longitudinal view across survey releases, identifying the key trends that have shaped the UK cyber landscape, and showing how apparent movement resolves into a stable, insecure equilibrium over time. - Article 3: The Gap Between Reality and Reporting
A structural model that overlays Breaches Survey, ICO, and NCSC data to reveal a deeper issue: that UK cyber risk is not directly observed, but filtered through layers of detection, reporting, and significance.
Taken together, these three perspectives move from observation, to trend, to model, and show that the real problem isn’t just cyber risk.
It’s how we measure it.
2. The Headline Numbers Hide the Real Signal
At a glance, the survey appears to offer stability. The numbers aren’t spiking, the narrative isn’t alarming, and there’s a sense, if you want to find it, that things might be under control.
But this is exactly where cyber analysis tends to go wrong: mistaking familiarity for progress.
- 43% of UK businesses experienced a cyber breach or attack in the last 12 months
- 28–30% of charities did the same
- For larger organisations:
- 65–69% of medium and large firms were breached
At first glance, this looks stable, perhaps even slightly improved from previous years.
But stability here is not success. It is persistent systemic exposure.
When nearly half of all organisations are breached annually, cyber risk is no longer an exception. It is the baseline operating condition of the UK economy.
3. The “Improvement” is Statistical, Not Structural
It’s tempting, especially for policymakers and commentators, to point to small improvements and frame them as evidence that interventions are working.
But in complex systems, small changes in metrics often reflect changes in measurement, not changes in reality.
The modest drop from ~50% to ~43% breach prevalence is often cited as progress.
It isn’t.
The reduction is largely attributed to fewer small businesses recognising phishing attacks, not necessarily fewer attacks occurring.
In other words:
The system hasn’t become more secure.
It has become less aware of its own insecurity.
This distinction matters enormously for policy, investment, and sector strategy.
Because if awareness is falling faster than risk, then the system is not improving; it is drifting out of alignment with reality.
4. Sectoral Reality: Size Matters More Than Capability
One of the most persistent myths in cyber security is that maturity scales cleanly with size, that larger organisations are simply “better” at security.
The survey data tells a more nuanced, and more uncomfortable, story.
- Large organisations: ~70% breach rate
- SMEs: significantly lower, but largely due to detection and reporting gaps
This exposes a core structural truth:
Cyber exposure scales with digital dependency, not necessarily with defensive maturity.
Large organisations:
- Have broader attack surfaces
- More complex supply chains
- Greater dependency on digital systems
But critically, they are also:
- Better at detection
- More transparent in reporting
So the “sectoral difference” is partly real risk, and partly measurement artefact.
Which means comparisons between sectors, or organisation sizes, often tell us less about security, and more about visibility.
5. The Attack Landscape Hasn’t Changed (Much)
There is a constant narrative in cyber: that the threat landscape is evolving rapidly, driven by new technologies, new actors, and new attack methods.
And yet, when you look at the data year after year, a different pattern emerges, one of remarkable consistency.
Despite all the noise around AI, zero trust, and next-gen tooling:
- Phishing remains dominant (still the most common and disruptive attack vector)
- Impersonation and account compromise follow
- Ransomware remains present but relatively low-volume in reported data (~1%)
This leads to an uncomfortable conclusion:
The UK cyber problem is not primarily technological.
It is behavioural, organisational, and economic.
We are still losing to attacks that are, in many cases, two decades old in technique.
This suggests that innovation in defence is not the limiting factor: adoption and execution are.
6. Governance is Improving… Slowly (and Too Late)
Over the past few years, there has been a clear push to elevate cyber security from an IT issue to a board-level concern.
That shift is happening, but not at the pace or depth required.
There are signs of movement:
- Board-level responsibility for cyber is increasing (~31%)
- Government pushing Cyber Essentials and resilience pledges
But this is incremental, not transformational.
At the same time:
- Only ~25% of organisations have formal incident response plans
- Only ~20% provide regular cyber training
This creates a dangerous mismatch:
Cyber is now a board-level risk… without board-level operational readiness.
In other words, accountability is rising faster than capability.
And in complex systems, that gap is where failures tend to emerge.
7. The Economic Reality: Cyber is Still Undervalued
To understand why these patterns persist, you have to step outside the technical domain and look at the underlying economics.
Because organisations are not failing to act randomly, they are responding to incentives.
Perhaps the most important insight for sectoral analysis:
- The cost of cyber insecurity is widely distributed and often indirect
- The cost of cyber investment is direct, immediate, and visible
So organisations rationally underinvest.
This is classic market failure:
- Externalities (supply chain risk, systemic disruption)
- Information asymmetry (unknown vulnerabilities)
- Misaligned incentives (short-term vs long-term risk)
Which explains why:
Even after years of guidance, frameworks, and awareness campaigns,
basic cyber hygiene is still not universal.
Until the incentive structure changes, the outcome won’t.
8. AI is Not the Disruption: It’s an Amplifier
AI is increasingly positioned as a transformative force in cyber security: either as a defensive breakthrough or an existential threat.
The reality, as usual, is more grounded.
The 2025/26 survey and surrounding commentary highlight AI as an emerging risk amplifier.
But AI is not fundamentally changing the problem space.
It is:
- Increasing attack scale and automation
- Improving social engineering quality
- Lowering the barrier to entry for attackers
Which means:
AI doesn’t create new vulnerabilities.
It industrialises existing ones.
So if the underlying system remains unchanged, AI will simply make its weaknesses more visible, more frequent, and more costly.
While AI is increasing the speed and scale of attacks, its primary effect is to amplify existing weaknesses, particularly in detection and human-factor vulnerabilities, rather than fundamentally changing the structure of cyber risk.
9. The Sectoral Insight: Cyber is a System, Not a Capability
Across this Cyber Sectoral Analysis series, a consistent theme has been emerging: that cyber security cannot be understood in isolation.
It is not a function you “install” into an organisation. It is a property of the system as a whole.
The Breaches Survey reinforces that:
- Organisations are individually rational but collectively vulnerable
- Supply chains remain under-secured
- Human factors dominate technical controls
- Detection ≠ prevention ≠ resilience
This reframes the problem:
Cyber resilience is not about:
- Tools
- Controls
- Compliance
It is about system design.
And until we design for resilience at the system level, improvements at the organisational level will remain partial and fragile.
10. What This Means for the UK Cyber Ecosystem
If you step back from the individual data points, a broader picture of the UK cyber ecosystem comes into focus.
And it is one defined less by failure, and more by incomplete transformation.
From a sectoral perspective, three implications stand out:
10.1 The “Long Tail” Problem Persists
Hundreds of thousands of SMEs remain:
- Under-protected
- Under-trained
- Under-incentivised
Yet they are deeply embedded in national supply chains.
This is not an edge case: it is the core structural risk.
10.2 Resilience is Becoming the Core Metric
The question is shifting from:
“Can we prevent breaches?”
to:
“Can we absorb and recover from them?”
This aligns directly with:
- NCSC resilience framing
- Emerging UK cyber policy direction
- The growing emphasis on testing and assurance
Which suggests a transition from security as protection to security as adaptation.
10.3 Measurement is Still Weak
Finally, and perhaps most critically, we are still operating with limited visibility.
We still lack:
- Reliable detection baselines
- Consistent reporting
- Clear economic impact models
Which means:
We are optimising a system we cannot fully observe.
And in any system, poor measurement leads to misplaced confidence.
10.4 The Policy Response
A clear policy response is emerging from this data: improving baseline cyber hygiene, increasing board-level accountability, and driving adoption of frameworks such as Cyber Essentials. These are necessary and rational interventions, particularly given the persistence of common attack vectors such as phishing.
However, they operate primarily at the level of what organisations can already see, measure, and manage. As the analysis in this article suggests, a significant portion of cyber risk sits below that layer, where detection is inconsistent, reporting is incomplete, and incentives remain misaligned. This creates a structural constraint: improvements in visible controls do not necessarily translate into reductions in underlying exposure.
11. Conclusion: A Plateau, Not Progress
Taken together, the findings of the Cyber Security Breaches Survey 2025/26 point to something subtle but significant.
Not crisis. Not collapse. Not even clear regression.
But a plateau.
A confirmation that the UK has reached a cyber security plateau.
- Breaches are widespread but normalised
- Defences are improving but uneven
- Awareness is rising but not translating into action
This is what maturity looks like in a misaligned system:
- Stable
- Predictable
- Still fundamentally insecure
12. Closing Thought for the Series
If the last decade was about raising awareness,
the next decade must be about changing incentives.
Because until cyber security becomes:
- economically rational
- operationally embedded
- systemically enforced
we will continue to measure the same numbers,
year after year,
and call it progress.