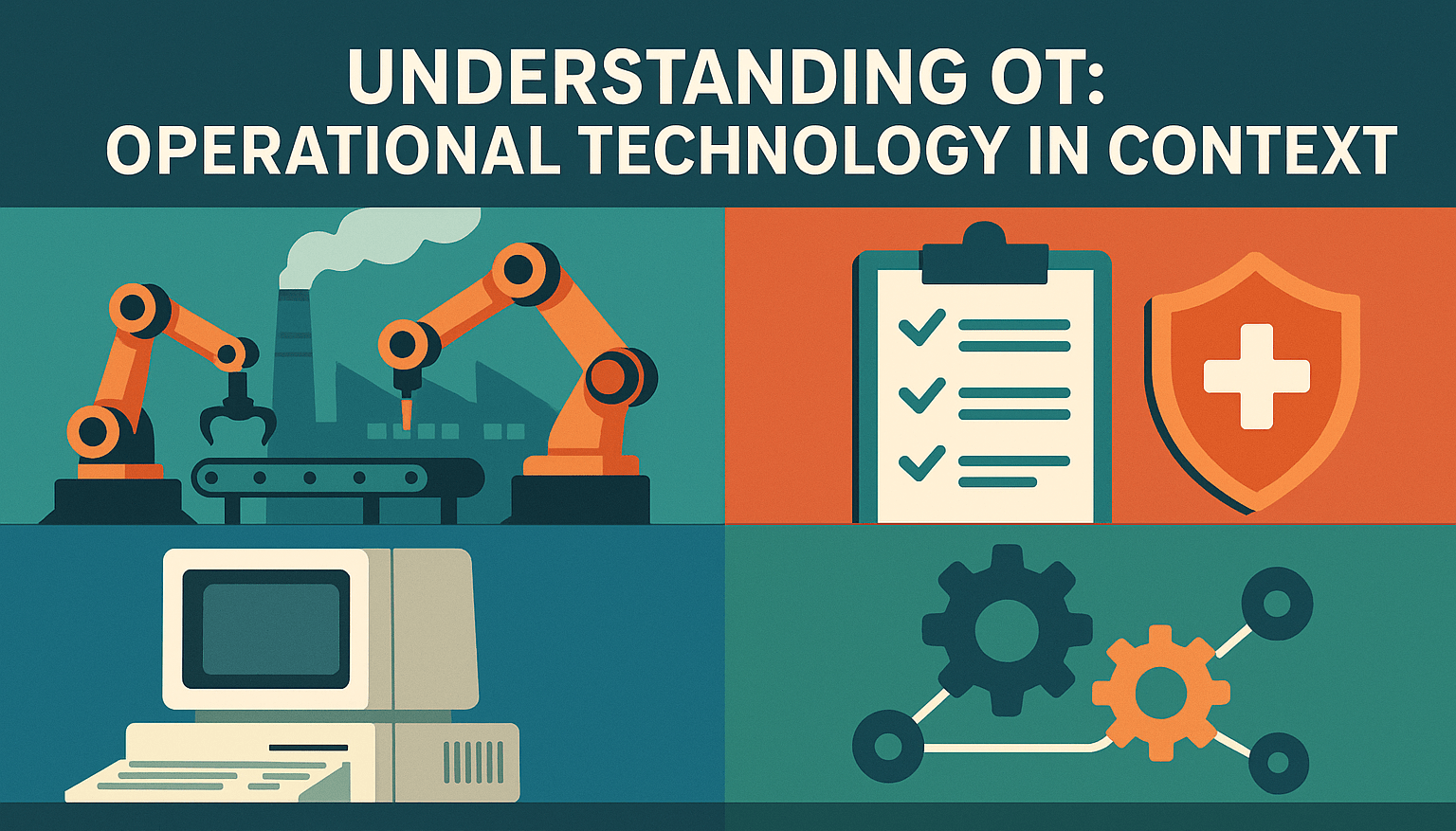
This article defines Operational Technology (OT) as distinct from traditional IT, highlighting its core characteristics, such as real-time control, safety-critical processes, long-lifecycle assets, and minimal security by design. It is the first in a short series of articles that argues that failure to recognise OT environments as such leads to systemic cybersecurity blind spots, particularly in sectors like healthcare, logistics, and building management.
Continue reading