Governments around the world are introducing age-verification and youth social-media laws, but these policies may be doing far more than protecting children. They are quietly pushing identity into operating systems, app stores, and the core infrastructure of the internet, shifting governance down the stack and creating new enforcement chokepoints. Along the way, they reshape platform power, favour large incumbents, and redefine how users access digital environments. As illustrated in “Evolution of Internet Architecture (1990–2035)”, this may signal a transition toward an “identity-mediated” web. This article documents those changes, drawing on historical precedents from UK identity systems (including the UK identity card programme) and US telecommunications, and comparative developments across multiple jurisdictions, to show how independent regulatory efforts are converging on a shared architectural shift.
Evolution of Internet Architecture (1990–2035) Diagram
The development of age verification infrastructure can be understood within a broader historical evolution of the internet. Early internet systems prioritised anonymous access and decentralised protocols. The rise of large social media platforms introduced centralised governance through algorithmic moderation. Emerging regulatory frameworks may now be pushing the internet toward a third phase in which identity attributes determine access to digital environments.
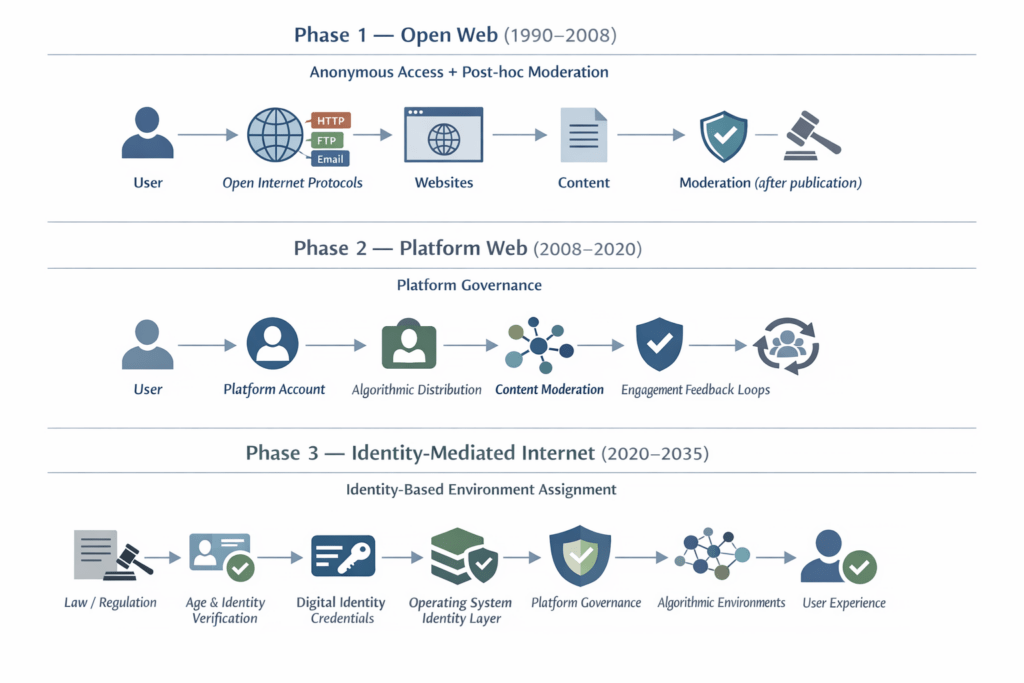
Structurally, these models align with the following primary control layer.
| Phase/ERA | Primary Control Layer and Aspects |
|---|---|
| Phase 1 (1990–2008): Open Web | Protocols: anonymous access and post-publication moderation. |
| Phase 2 (2008–2020): Platform Web | Platforms: centralise governance via accounts and algorithms. |
| Phase 3 (2020–2035): Identity-Mediated Web | Identity Infrastructure: Verifies user attributes (starting with age), that gate access and shape environments before interaction. |
Executive Summary
Over the past several years, governments around the world have introduced a growing number of laws aimed at protecting children online. These include social media age restrictions, online safety legislation, and requirements for platforms to prevent minors from accessing harmful content.
Taken individually, these policies appear to address specific problems within particular jurisdictions. Viewed collectively, however, they reveal a broader shift in how the internet itself is being governed.
Historically, the internet operated as an open network in which users could participate anonymously, and content moderation occurred after information was published. The emerging regulatory model increasingly reverses that relationship. Instead of moderating content after interaction occurs, platforms are being required to classify users, most commonly by age, before determining what digital environments they may access.
This shift is driving the development of new technical infrastructure across several layers of the technology stack. Age verification systems, digital identity credentials, operating-system identity services, and platform governance frameworks are gradually combining into a layered architecture in which user attributes shape the information environments users encounter online.
In practice, this means that the internet is beginning to move from a model of open access followed by moderation toward one of identity-mediated access and environment design. Age verification legislation may therefore represent the first large-scale deployment of identity attributes as infrastructure within the operational architecture of the internet.
The infrastructure emerging around age verification and operating-system identity layers can also be understood through the lens of Digital Public Infrastructure (DPI). DPI frameworks typically describe three foundational capabilities that enable participation in digital society: authentication (identity), transactions (payments), and data exchange between institutions.
Age verification systems represent a specialised form of authentication infrastructure embedded directly into the operational stack of the internet. When identity attributes become embedded within browsers, operating systems, and digital identity wallets, they begin to function not merely as regulatory compliance mechanisms but as components of a broader infrastructure for governing digital participation. Age verification is the first identity attribute to be widely deployed within this emerging system, but the infrastructure being built could support additional forms of classification in the future.
This article examines the legislative origins of this shift, the technical mechanisms being developed to implement it, and the broader implications for anonymity, platform power, algorithmic governance, and the future structure of the web.
The central argument is not that governments are intentionally redesigning the internet. Rather, the interaction between child-safety regulation, platform governance, and identity infrastructure is gradually producing a new form of digital architecture: one in which identity attributes, platform rules, and algorithmic systems increasingly operate together to structure online environments.
Understanding this transition is essential for evaluating the long-term consequences of the current wave of age-verification laws.
Contents
- Evolution of Internet Architecture (1990–2035) Diagram
- Executive Summary
- Contents
- Abstract
- 1. Introduction: The Sudden Appearance of an Age-Gated Internet
- 2. The Legislative Landscape
- 3. Timeline of the Global Age-Verification Wave (2015–2026)
- 3.1 2015–2016: The Pornography Problem
- 3.2 2017: The UK Digital Economy Act
- 3.3 2019: Collapse of the First Generation
- 3.4 2020–2021: From Pornography to “Online Safety”
- 3.5 2022: The Rise of Platform Governance
- 3.6 2023: The Online Safety Act
- 3.7 2024: Expansion Across the United States
- 3.8 2025: Enforcement Begins
- 3.9 2026: Global Expansion and Circumvention
- 4. The ID Card Debate in the United Kingdom: A Long Political “Debaclate”
- 4.1 Wartime Identity Cards and Their Abolition
- 4.2 The Modern Origins of the UK Identity Card Debate
- 4.3 The Identity Cards Act 2006
- 4.4 The Limited Success of Digital Identity: the Government Gateway
- 4.5 The Failure of Digital Identity: GOV.UK Verify
- 4.6 Delegated Authority and the Next Generation of Digital Identity
- 4.7 Security, Requirements, and the Practical Challenges of Identity Infrastructure
- 4.8 The European Contrast: France and Germany
- 4.9 Why the UK Debate Is Different
- 4.10 From ID Cards to Digital Identity
- 4.11 And onto Age Verification
- 4.12 The Reality of Identity in the UK: De Facto Systems and Structural Gaps
- 5. What People Think Is Happening
- 5.1 Narrative A: Child Protection
- 5.2 Narrative B: The “Censorship Industrial Complex”
- 5.3 Narrative C: Advertising Markets and Bot Detection
- 5.4 Narrative D: Platforms Shifting Verification to Infrastructure
- 5.5 The Limits of These Narratives
- 5.6 Emerging Policy Debate
- 5.7 Moderation vs. Environment Design
- 5.8 A Historical Precedent: Governance Migration in Telecommunications
- 5.9 Motivations and Structural Outcomes
- 6. What Is Actually Being Built
- 6.1 The Downward Migration of Internet Governance
- 6.2 The Old Internet
- 6.3 The Emerging Internet
- 6.4 Identity as Infrastructure
- 6.5 Diverging Architectural Directions
- 6.6 Competing Models of Identity Infrastructure
- 6.7 Attribute Proof Rather Than Disclosure
- 6.8 The Internet’s Anti-Identity Origins
- 6.9 Environment Design
- 6.10 Evaluating the Emerging Identity-Mediated Internet as Digital Public Infrastructure (DPI)
- 7. How OS-Level Age Verification APIs Work
- 8. Why Governments Target Operating Systems
- 9. Technical Challenges and Circumvention
- 10. Economic Incentives Behind the System
- 11. Behavioural Collapse and Identity Signals
- 12. Asymmetric Integration and the Post-LLM Web
- 13. The Internet Architecture Now Emerging: Part 1: Conceptual Explanation
- 13.1 Why Age Verification Appeared Everywhere at Once
- 13.2 Age Verification as the First Identity Attribute
- 13.3 Toward a KYC-Style Attribute Governance Model for the Internet
- 13.4 The Convergence of AI Governance, Platform Governance, and Age Verification
- 13.5 Uncoordinated Change Can Still Produce Structural Transformation
- 13.6 Geopolitical Convergence: Why Every Major Power Wants the Same Stack
- 14. The Internet Architecture Now Emerging II: System Architecture Walkthrough
- 15. Does This Actually Protect the People It Claims To?
- 16. Implications for the Future of the Internet
- 17. Conclusion: What Architecture Is Emerging?
- 18. Appendices
- 18.1 Appendix A: Global Map of Age Verification Laws
- 18.2 Appendix B: Technical Implementation Models
- 18.3 Appendix C: An Infrastructure Still in Formation
- 18.4 Appendix D: Bibliography
- 18.4.1 Legislation and Regulatory Frameworks
- 18.4.2 Digital Platform Governance and Regulation
- 18.4.3 Identity Infrastructure and Digital Identity Theory
- 18.4.4 Surveillance Capitalism and Algorithmic Governance
- 18.4.5 Youth Online Safety and Social Media Research
- 18.4.6 Internet Governance and Platform Power
- 18.5 Appendix E: Media, Government Reports, and Institutional Sources
- 18.6 Appendix F: Optional Suggested Reading
- 18.7 Appendix G: Media Timeline of Age-Verification and Online Safety Regulation (2015–2026)
- 18.7.1 2015–2017 — First Wave: Pornography Age Verification
- 18.7.2 2018–2019 — Collapse of the First Age Verification System
- 18.7.3 2020–2021 — Platform Harm Debate and Whistleblowers
- 18.7.4 2022 — Platform Governance Legislation
- 18.7.5 2023 — Online Safety Frameworks
- 18.7.6 2024 — Youth Social Media Laws
- 18.7.7 2025 — Enforcement Begins
- 18.7.8 2026 — Global Expansion and Infrastructure Debate
Abstract
Age verification laws introduced to protect children online are often debated as isolated regulatory interventions. This article argues that they represent something more significant: the early stages of a structural shift in the architecture of the internet.
Across multiple jurisdictions, governments are requiring digital platforms to prevent minors from accessing certain forms of online content. To enforce these obligations at scale, platforms must obtain reliable information about users’ identities, particularly their age. The technical mechanisms developed to provide this information increasingly involve operating system identity frameworks, cryptographic credentials, and digital identity infrastructure.
This article examines how these developments are embedding identity attributes into the technological layers through which digital services operate. The result is the emergence of what the paper describes as an identity-mediated internet architecture, in which digital environments are configured according to verified user attributes before interaction occurs.
Seen in isolation, age verification appears to be a narrow regulatory tool. Seen in architectural context, it represents the first widely deployed identity signal within a system that may increasingly organise digital environments around identity, governance, and algorithmic optimisation.
1. Introduction: The Sudden Appearance of an Age-Gated Internet
For most of the past three decades, the internet has operated on a remarkably simple social contract: access first, identity later, if at all. A user could arrive at a website, forum, or social platform with little more than a browser and a connection. Identity was optional, anonymity common, and verification rare. While certain domains (banking, government services, enterprise networks) required authentication, the broader informational web largely did not.
That assumption is now quietly dissolving.
Over the past eighteen to twenty-four months, a cluster of regulatory initiatives has begun appearing across multiple jurisdictions. Taken individually, these policies appear modest: a youth-protection law in one country, a platform safety regulation in another, a proposed age-verification scheme somewhere else. Yet when examined collectively, they reveal something more substantial. Governments around the world are beginning to restructure how access to digital services is mediated.
The shift is not happening through a single grand legislative project. Rather, it is emerging through a convergence of policy initiatives that (while framed differently in different regions) tend toward the same underlying mechanism: systems that determine who a user is, or at least what category of person they belong to, before granting access to online services.
Across jurisdictions, the new regulatory wave generally falls into several overlapping categories:
- Social media bans or restrictions for minors often prohibit accounts below a certain age or require parental consent.
- Operating-system-level age verification mandates require devices to expose age signals to apps and services.
- Platform “duty of care” regimes obliging digital platforms to actively protect minors from certain types of content or algorithmic exposure.
- Digital identity infrastructures, including government-backed identity wallets and verified credentials.
- Algorithmic safety regulations require platforms to adjust recommendation systems for children and vulnerable users.
Many of these laws are scheduled to come fully into force between 2025 and 2027, a relatively compressed implementation window for policies that potentially affect billions of internet users.
What makes the phenomenon particularly difficult to perceive in real time is that each policy is framed in narrowly local terms. A national parliament debates youth mental health. A state legislature responds to concerns about online pornography. A regulatory agency updates child-safety guidelines. Each measure appears to address a discrete problem within a specific jurisdiction.
Viewed from a distance, however, the pattern is unmistakable.
Across North America, Europe, Australia, and parts of Asia, policymakers are gradually constructing a regulatory environment in which access to digital platforms increasingly depends on the verification of certain user attributes, most commonly age, but potentially others in the future. The individual initiatives differ in scope and mechanism, yet they converge on the same operational premise: platforms cannot regulate user experiences without knowing something about the user.
The result is the quiet emergence of what might be called an age-gated internet.
This term should not be understood narrowly as referring only to pornography filters or parental controls. Instead, it describes a broader architectural transition in which online services increasingly require systems capable of determining whether a user is a child, a teenager, or an adult before deciding what content, features, or algorithmic pathways that user may access.
The deeper shift can be summarised in a single observation:
Multiple regions of the world are moving toward identity-mediated access to digital services.
In such a system, the internet does not simply respond to requests for information. It first classifies the requesting entity. Only then does it determine what the user is permitted to see, do, or participate in.
This development represents a subtle but profound departure from the original architecture of the web. The early internet assumed that information flows could be moderated after publication, through community moderation, legal intervention, or platform governance. The emerging model assumes something different: that digital environments must be structured around categories of users before interaction occurs.
Age verification is the most politically acceptable entry point for this transformation. Few policymakers are willing to defend unrestricted access to harmful material for children. As a result, legislation framed around child protection encounters relatively little resistance. Yet once the technical infrastructure for verifying age exists, it becomes possible to extend the same mechanisms to other forms of classification.
For this reason, the current regulatory wave should not be understood solely as a set of youth-protection measures. It is also the early stage of a broader reconfiguration of how identity, platforms, and governance intersect on the internet.
The transformation is still incomplete. Many of the systems required to implement these laws, verification technologies, operating-system interfaces, and digital credential frameworks remain under development. Legal challenges continue in several jurisdictions. Technical feasibility remains contested.
Nevertheless, the direction of travel is increasingly clear. The internet is beginning to evolve from an environment where users could arrive anonymously and negotiate identity later, into one where identity attributes increasingly shape access from the outset.
How that shift occurred, and what it ultimately implies, requires examining both the legislative landscape and the technological systems that are emerging to support it.
This paper argues that the infrastructure emerging around age verification and online safety regulation is quietly transforming the architecture of the internet and how contemporary child safety legislation is contributing to the emergence of the third architectural phase illustrated in Figure 1, “Evolution of Internet Architecture (1990–2035)”.
This article refers to this emerging system as an identity-mediated internet architecture. In such systems, identity attributes are embedded within operating systems, identity infrastructure, and digital platforms, enabling services to classify users and configure digital environments before interaction occurs.
The open web model, where anyone could access services anonymously, and moderation occurred after the fact, is being replaced by identity-mediated environments in which users are classified before interaction occurs.
1.1 Age Verification as the First Identity Attribute
One of the central claims of this paper is that age verification should not be understood primarily as a narrow child-safety policy. Rather, it represents the first large-scale deployment of a verified identity attribute within the operational infrastructure of the modern internet.
Historically, the web functioned largely without embedded identity infrastructure. Users arrived at websites anonymously or under pseudonyms, and platforms moderated behaviour and content after interaction occurred. Identity attributes were optional and generally confined to specific domains such as banking, government services, or enterprise networks.
Age verification changes this architectural assumption.
When platforms are required to determine whether a user is a minor before granting access to certain features or content, they must obtain a reliable signal about the user’s age category. Once that signal exists, it becomes reusable across multiple services and systems.
In other words, age becomes an identity attribute embedded within digital infrastructure.
The significance of this shift lies not in the attribute itself but in the precedent it establishes. Once infrastructure exists for verifying and transmitting one attribute, such as age, the same mechanisms can support additional attributes in the future. These may include jurisdiction, identity verification status, professional credentials, or other forms of eligibility verification.
Age verification is therefore best understood as the first widely deployed identity signal within a broader architectural transition toward identity-mediated digital environments.
2. The Legislative Landscape
If the emergence of an age-gated internet appears sudden, the explanation lies partly in how the relevant legislation has developed. Rather than arising from a single international framework or coordinated regulatory regime, the legal architecture has evolved through a patchwork of national and regional initiatives. Each jurisdiction has addressed what it perceives to be a local problem, youth mental health, online pornography, algorithmic harms, or platform accountability. Yet the resulting legal frameworks share a common feature: they all require some mechanism for determining the age, or at least the age category, of the user.
The cumulative effect is not merely regulatory overlap but a converging global architecture. Governments that differ widely in political systems, legal traditions, and technological ecosystems are nevertheless arriving at broadly similar policy conclusions. Platforms cannot meaningfully protect children online, regulators argue, unless they can determine whether the user is in fact a child.
The legislative landscape therefore represents the first concrete layer of the shift toward identity-mediated digital services.
2.1 United States
In the United States, the regulatory picture is unusually fragmented. Unlike the European Union or the United Kingdom, the federal government has not yet established a comprehensive national framework governing youth access to social media or age verification online. Instead, regulation has emerged through a growing number of state-level initiatives.
These laws vary significantly in design and scope. Some focus on social media access; others target adult content or platform duty-of-care requirements. Most combine elements of both.
Several states have enacted or proposed legislation within the past two years:
| State | Law / Policy | Approach |
|---|---|---|
| California | Digital Age Assurance Act | Age estimation / safety by design |
| Florida | HB3 | Social media age restrictions |
| Utah | Social Media Regulation Act | Parental consent |
| Nebraska | Youth online safety proposals | Parental consent model |
| Louisiana | Pornography age verification | Content access restriction |
| Mississippi | Pornography age verification | Content access restriction |
| Virginia | Youth social media rules | Age estimation/safety by design |
The underlying regulatory strategies differ. Some states attempt to prohibit minors from accessing specific services entirely, while others impose parental consent models or time-based restrictions. Still others focus on forcing platforms to implement age-verification mechanisms before allowing access to certain categories of content.
What unites these laws is the assumption that platforms must determine the age status of their users before enforcing regulatory obligations.
Many of these initiatives remain under constitutional challenge. Courts have been asked to consider whether mandatory age verification or youth social media restrictions violate First Amendment protections or impose unreasonable burdens on speech and privacy. Several early laws have already faced injunctions or revisions, suggesting that the American regulatory landscape will continue to evolve through litigation as much as legislation.
Nonetheless, the direction is clear. In the absence of federal policy, state governments have begun experimenting with multiple regulatory models simultaneously.
Despite this fragmentation, American regulation still has global consequences. Most of the world’s dominant technology platforms are headquartered in the United States, including Apple, Google, Meta, and Microsoft. If compliance with state-level age verification laws requires new forms of age signaling at the operating-system or app-store level, those mechanisms may be implemented globally rather than limited to individual jurisdictions. As a result, even decentralized state regulation in the United States may contribute to the emergence of shared technical infrastructure across the internet.
2.2 Europe
Europe presents a more structured legislative environment, largely due to the regulatory role of the European Union and the historically stronger relationship between digital governance and public policy.
Two major frameworks dominate the European approach: the EU Digital Services Act and the UK Online Safety Act.
The Digital Services Act (DSA) establishes a comprehensive regulatory regime for large online platforms operating within the European Union. Rather than mandating specific verification technologies, the DSA imposes a system of risk management obligations. Platforms must identify and mitigate systemic risks associated with their services, including risks affecting minors.
These obligations include requirements to:
- assess systemic platform risks
- implement safeguards protecting children
- mitigate exposure to harmful content
- increase transparency around algorithmic systems.
While the DSA does not explicitly mandate universal age verification, it effectively requires platforms to deploy mechanisms capable of distinguishing between adult and minor users if they are to satisfy their obligations under the law.
The United Kingdom has adopted a more direct regulatory approach through the Online Safety Act, passed in 2023. The law requires platforms hosting potentially harmful content to implement what regulators describe as “highly effective age assurance.”
This requirement applies particularly to categories of content considered dangerous for minors, including:
- pornography
- self-harm content
- suicide-related material
- eating disorder content.
In practice, this pushes platforms toward implementing age verification technologies or equivalent mechanisms capable of distinguishing minors from adults.
Beyond these two major frameworks, several European countries have begun introducing additional youth protection laws.
| Country | Policy Focus |
|---|---|
| France | Social media access requires parental consent under 15 |
| Spain | Proposed social media restrictions for minors |
| Denmark | Youth social media access limits under consideration |
| Norway | Proposed minimum social media age of 15 |
These initiatives vary widely in detail, but they share the same structural premise: platforms must possess reliable information about the age category of their users.
2.3 Australia
Among democratic nations, Australia has arguably taken the most aggressive legislative stance.
The country has introduced what is widely described as the world’s first nationwide social media ban for users under the age of sixteen. Under the proposed regulatory framework, major social platforms are required to ensure that minors below this threshold cannot create accounts.
In practical terms, this means platforms must implement mechanisms capable of verifying whether a user is over sixteen before allowing access.
Unlike parental consent models adopted elsewhere, the Australian system places primary responsibility on the platform rather than the parent or user. Failure to enforce the rule can result in significant financial penalties.
The policy has attracted both strong support and significant criticism. Supporters argue that it represents a necessary intervention to address youth mental health concerns and social media addiction. Critics contend that the law may be technically unenforceable and risks encouraging intrusive verification technologies.
Regardless of its long-term effectiveness, the Australian initiative marks an important regulatory milestone: it demonstrates the willingness of governments to move beyond content restrictions toward direct control of platform access based on user age.
2.4 Global Adoption
The trend is not limited to a handful of Western democracies. Age-verification frameworks or youth access restrictions are now appearing across a diverse range of political and technological environments.
Countries currently implementing or considering such systems include:
- United Kingdom
- Australia
- Germany
- France
- Spain
- Norway
- South Korea
- China
- United Arab Emirates
- Saudi Arabia
- Brazil
- Mexico
In some of these countries, age verification emerges through youth safety legislation. In others, it forms part of broader identity or telecommunications regulation. Several nations in Asia and the Middle East already operate digital systems in which real-name registration or national identity verification is required for certain online services, making age verification a relatively straightforward extension.
The resulting picture is not one of uniform policy but of converging regulatory strategies. Governments with very different political philosophies are increasingly arriving at the same operational requirement: if platforms must regulate content exposure for children, they must first determine whether the user is a child.
2.5 Major Age-Verification Laws
| Country | Law | Scope |
|---|---|---|
| United Kingdom | Online Safety Act | Harmful online content |
| Australia | Social media age ban | Users under 16 |
| France | Youth social media law | Users under 15 |
| United States (various states) | Multiple state laws | Social media and adult content |
Seen collectively, these laws reveal something important. Age verification is not emerging as a niche policy limited to pornography regulation or parental control systems. It is becoming a central component of the broader effort to regulate digital platforms.
Once this shift is recognised, the next question naturally arises: how did the policy momentum build so quickly?
To answer that, we must look back at the evolution of the idea itself.
3. Timeline of the Global Age-Verification Wave (2015–2026)
Technological transformations rarely arrive in a single decisive moment. More often, they accumulate through a sequence of experiments, failures, reframings, and institutional learning. The emergence of age verification as a central instrument of internet governance follows this pattern precisely. What now appears as a coordinated regulatory wave was, in reality, assembled over nearly a decade through a series of policy iterations.
Understanding this trajectory matters. The shift toward identity-mediated internet access did not arise suddenly from a single legislative innovation. It emerged gradually as policymakers attempted, often unsuccessfully, to regulate specific harms within the architecture of an open, largely anonymous network.
The period from roughly 2015 to 2026, therefore, represents a formative phase in which the concept of age verification evolved from a narrowly targeted tool for restricting adult content into a broader mechanism for structuring platform governance itself.
3.1 2015–2016: The Pornography Problem
The earliest modern age-verification proposals were almost entirely focused on a single issue: children accessing online pornography.
By the mid-2010s, policymakers across several countries had become increasingly concerned about the ease with which minors could access explicit material online. Parliamentary inquiries and public consultations began exploring mechanisms for restricting such access.
The technological proposals discussed at the time were relatively blunt instruments. Among the options considered were:
- credit-card verification systems that would restrict adult sites to users with valid payment credentials
- national identity databases capable of verifying a user’s age before granting access to restricted content
- age-check gateways operated by third-party verification providers.
These proposals reflected an early assumption that regulating specific types of websites would be sufficient. The broader architecture of the internet itself was not yet under consideration.
At this stage, age verification was seen primarily as a content gatekeeping mechanism, not as a general framework for regulating digital platforms.
3.2 2017: The UK Digital Economy Act
The first serious attempt to implement such a system arrived with the United Kingdom’s Digital Economy Act of 2017. The law required commercial pornography websites accessible from the UK to implement robust age verification mechanisms.
The policy was ambitious. Websites failing to comply could face:
- financial penalties
- payment processor restrictions
- potential ISP-level blocking.
For the first time, a national government attempted to mandate age verification across a major category of online services.
In principle, the system appeared straightforward. In practice, it proved extraordinarily difficult to implement.
3.3 2019: Collapse of the First Generation
By 2019, the British age-verification initiative had effectively collapsed.
Several problems became immediately apparent:
- Privacy concerns. Critics warned that centralised age-verification systems could create databases linking individuals to their consumption of explicit material, an obvious target for data breaches or abuse.
- Technical difficulties. Implementing verification across thousands of international websites proved far more complex than anticipated.
- Industry resistance. Many platforms argued that compliance requirements were unclear, expensive, or technically infeasible.
Facing mounting criticism and practical implementation barriers, the UK government ultimately abandoned the initiative.
At the time, the collapse was widely interpreted as a failure of age-verification policy itself. In retrospect, it represented something else: the failure of the first generation of regulatory thinking.
Rather than disappearing, the concept would soon return in a different form.
3.4 2020–2021: From Pornography to “Online Safety”
Following the failure of early porn-site verification schemes, policymakers reframed the problem.
The issue was no longer presented as access to pornography alone. Instead, regulators increasingly spoke about online harms affecting children more broadly. These included exposure to self-harm content, eating disorder communities, grooming risks, and algorithmically amplified harmful material.
Two major regulatory projects emerged from this reframing.
In the United Kingdom, the government began developing what would eventually become the Online Safety Bill, a far more comprehensive framework for regulating digital platforms.
At the European level, policymakers began drafting the Digital Services Act (DSA), which introduced a new model of systemic platform oversight.
The key conceptual shift was subtle but profound. Rather than attempting to block specific categories of websites, regulators began to ask whether platforms themselves should bear responsibility for identifying and mitigating risks affecting minors.
This question would reshape the entire regulatory landscape.
3.5 2022: The Rise of Platform Governance
By 2022, a new regulatory paradigm had begun to take shape.
Earlier approaches relied on content takedowns, removing harmful material once it had been identified. The emerging framework instead treated platforms as complex systems capable of generating societal risks through their design, algorithms, and recommendation structures.
Regulators, therefore, began focusing on systemic risk management.
Under this model, platforms must actively assess and mitigate risks generated by their services. If certain categories of content are harmful to children, the platform must prevent minors from encountering them.
But this logic immediately creates a practical requirement: platforms must know whether a given user is a minor.
Age verification, once confined to pornography regulation, suddenly became relevant to the governance of entire digital ecosystems.
3.6 2023: The Online Safety Act
The United Kingdom became the first country to formalize this shift through the Online Safety Act, passed in 2023.
The law requires platforms hosting potentially harmful content to implement “highly effective age assurance” systems. While the legislation does not mandate a specific technical solution, it establishes a clear expectation: platforms must be able to distinguish between adult and minor users.
This requirement applies to content involving:
- pornography
- self-harm or suicide
- eating disorders
- other forms of potentially harmful material.
The Act represents a turning point. Age verification was no longer a narrow tool targeting adult websites; it had become a foundational component of platform regulation.
3.7 2024: Expansion Across the United States
By 2024 the regulatory momentum began spreading rapidly across the United States.
A growing number of state legislatures introduced laws addressing youth access to online services. Some focused on pornography websites; others targeted social media platforms directly.
The result was a patchwork of state-level initiatives, each experimenting with different models of verification and restriction.
While the legal outcomes remained uncertain, many laws faced immediate constitutional challenges, the political signal was unmistakable. Age verification had become a mainstream regulatory idea rather than a fringe proposal.
At the same time, policymakers in several other countries began drafting similar laws, accelerating what now appears to be a global policy diffusion process.
3.8 2025: Enforcement Begins
By 2025 the first major enforcement mechanisms began to take effect.
Platforms operating in the United Kingdom and other jurisdictions started deploying practical verification systems. These included:
- facial age-estimation technology
- government ID verification services
- credit-card-based verification mechanisms.
These tools were far from perfect. Critics raised concerns about accuracy, privacy, and the potential normalization of biometric verification online. Nevertheless, the systems marked the first large-scale implementation of age verification across major digital platforms.
The infrastructure that had remained largely theoretical for several years was now being deployed in production environments.
3.9 2026: Global Expansion and Circumvention
By 2026 age verification had become a common feature of digital governance debates across multiple regions.
Some platforms chose to comply with new regulations. Others took a different approach: restricting access entirely in jurisdictions where compliance proved too burdensome.
At the same time, users began adapting to the new environment. Reports of circumvention methods increased, including the use of VPNs and other tools to bypass geographic restrictions.
The result is a regulatory ecosystem still in flux. Governments continue expanding age-verification requirements, platforms continue experimenting with implementation strategies, and users continue searching for ways around the restrictions.
What is clear, however, is that the idea itself has survived every early failure. The concept that once appeared limited to blocking pornography has evolved into a central instrument for governing digital platforms.
The question is no longer whether age verification will play a role in internet governance. The question is how far the architecture built around it will extend.
4. The ID Card Debate in the United Kingdom: A Long Political “Debaclate”
The debate over identity systems in the United Kingdom has a long and unusually contentious history. Unlike many European countries, where national identity cards are routine administrative tools, attempts to introduce comprehensive identity systems in Britain have repeatedly triggered political backlash and eventual abandonment. The result is a recurring policy “debacle”, or perhaps more fittingly, a debaclate: a cycle in which governments attempt to introduce identity infrastructure only for the proposals to collapse under political and institutional pressure.
This pattern has recurred across multiple generations of policy. Wartime identity cards were abolished in 1952 after public resistance; the Identity Cards Act 2006 was repealed in 2010 after fierce political opposition; and more recently, the government’s flagship digital identity programme, GOV.UK Verify was quietly abandoned after failing to achieve adoption. Understanding this history is important because it shapes how contemporary debates over digital identity, age verification, and online safety are perceived in the UK.
4.1 Wartime Identity Cards and Their Abolition
Britain first introduced a national identity card system during the Second World War.
The National Registration Act 1939 required residents to register with the government and carry identity cards. The system was intended primarily for wartime administration, including:
- rationing
- population management
- national security.
After the war the system remained in place, but public acceptance eroded. The decisive turning point came in 1950, when a motorist named Clarence Willcock refused to present his identity card to a police officer. The case ultimately reached the courts, and although Willcock lost the case, the judge strongly criticised the government for using wartime identity powers in peacetime.
Public opinion shifted rapidly. In 1952 the government abolished the identity card system, citing public hostility and declining administrative value.
This episode established an enduring political norm: identity cards were seen as incompatible with British civil liberties traditions.
4.2 The Modern Origins of the UK Identity Card Debate
Although the UK abolished wartime identity cards in 1952, the modern political controversy around identity infrastructure largely began decades later in the late 1990s and early 2000s. Following growing concerns about immigration control, welfare fraud, and national security, the Labour government under Tony Blair began exploring the possibility of introducing a modern national identity system.
In 2002 the government published a consultation paper proposing a national identity card scheme linked to a centralised population register. The proposal gained additional political momentum after the terrorist attacks of September 11, 2001, as policymakers increasingly framed identity infrastructure as part of a broader security strategy.
The eventual Identity Cards Act 2006 created a legal framework for biometric identity cards and a National Identity Register intended to hold personal and biometric information for residents of the UK. Supporters argued that the system could strengthen border control, reduce identity fraud, and simplify interactions with public services.
However, the proposal quickly became one of the most controversial digital policy initiatives in modern British politics. Civil liberties organisations, technology experts, and opposition politicians raised concerns about privacy, surveillance, cost, and the risks associated with maintaining large centralised identity databases.
When the coalition government took office in 2010, the programme was rapidly dismantled. The Identity Documents Act 2010 repealed the identity card legislation and ordered the destruction of the National Identity Register.
The collapse of the programme reinforced a powerful political narrative: large-scale identity infrastructure in the UK was both technically risky and politically toxic. This legacy continues to shape contemporary debates around digital identity, age verification, and online authentication systems.
4.3 The Identity Cards Act 2006
The debate resurfaced in the early 2000s following the September 11 attacks and rising concerns about terrorism and immigration control.
The Labour government under Tony Blair proposed a modern national identity system that would combine:
- biometric identity cards
- a national identity register
- integrated government databases.
The proposal was enacted through the Identity Cards Act 2006.
The system was ambitious. It envisioned:
- biometric identity cards
- a centralised identity database
- integration with passports and immigration systems.
However, the proposal faced sustained criticism from across the political spectrum. Critics argued that the system would:
- expand state surveillance
- create large government databases vulnerable to abuse
- erode long-standing traditions of anonymity in public life.
The programme also encountered significant technical and financial challenges.
When the coalition government took office in 2010, it moved quickly to repeal the legislation. The Identity Documents Act 2010 abolished the identity card programme and destroyed the national identity register.
The episode reinforced the perception that national identity systems were politically toxic in the UK.
4.4 The Limited Success of Digital Identity: the Government Gateway
Before the GOV.UK Verify programme, the UK government had already deployed a large-scale digital authentication system known as Government Gateway. Introduced in the early 2000s, Government Gateway provided login credentials for accessing a range of public services, most notably online tax filing through HM Revenue & Customs.
Millions of individuals and businesses used Government Gateway IDs to interact with government systems, making it one of the earliest widely adopted digital identity mechanisms in the UK. While the system functioned primarily as an authentication service rather than a full identity assurance framework, it demonstrated that citizens were willing to use digital credentials for government services. The later GOV.UK Verify initiative attempted to build on this foundation by introducing stronger identity verification through third-party providers, but it ultimately struggled to achieve the same level of adoption.
In hindsight, Government Gateway illustrated a recurring pattern in the UK: relatively successful authentication systems exist, but attempts to expand them into comprehensive national identity infrastructure tend to encounter political and institutional resistance.
4.5 The Failure of Digital Identity: GOV.UK Verify
Attempts to build digital identity infrastructure also struggled.
The government’s flagship digital identity system, GOV.UK Verify, was launched to allow citizens to access public services online using private-sector identity providers. However, the programme never achieved widespread adoption.
A parliamentary review later concluded that the system was failing to meet its objectives, citing low user uptake and technical limitations.
This failure reinforced skepticism toward government-led identity infrastructure.
4.6 Delegated Authority and the Next Generation of Digital Identity
Recent policy discussions have shifted toward a more decentralised model of digital identity.
The UK government’s digital verification services trust framework introduces the concept of delegated authority, where individuals can authorise trusted digital services to act on their behalf. This model attempts to avoid the political and technical pitfalls of earlier centralised identity schemes.
Recent consultations on digital identity policy suggest the government is again exploring ways to integrate identity systems into public services, including authentication for accessing government services online.
However, the history of repeated identity system failures means that such proposals are likely to remain politically sensitive.
The current UK digital identity programme is led within the Government Digital Service by the Digital Identity team, which has been tasked with developing the UK’s digital identity trust framework and related verification services.
4.7 Security, Requirements, and the Practical Challenges of Identity Infrastructure
One of the most common objections raised during debates about national identity systems is the fear that such systems will inevitably be hacked or compromised. Critics frequently argue that a centralised identity infrastructure would create a single point of failure in which sensitive personal data could be exposed if the system were breached.
However, this argument often overlooks an important factor: the security of a system is not determined solely by its architecture but also by the quality of its design and implementation. Secure systems are the result of careful engineering, rigorous policy design, and disciplined development practices. When identity systems are designed with clear security models, strong operational controls, and well-defined trust frameworks, they can be highly resilient.
For example, the Government Gateway, which has served as the authentication system for UK public services such as HMRC online tax filing since the early 2000s, has operated for many years without major public breaches of its core infrastructure. Systems like this demonstrate that secure digital authentication platforms are achievable when sufficient attention is given to design, governance, and operational security.
A second challenge arises from the political environment surrounding identity systems. Debates about civil liberties and surveillance often expand the scope of proposed systems by introducing increasingly complex requirements intended to satisfy multiple policy concerns simultaneously. These expanding requirements can significantly complicate the design and implementation of identity infrastructure, increasing cost and risk.
A third issue concerns institutional continuity. Large digital identity programmes often rely on the same organisational teams that worked on earlier projects. When previous programmes have struggled or failed, simply extending the same organisational structures into new initiatives may not address underlying problems in governance, design approach, or technical capability.
Finally, there is the tendency for governments to overload identity systems with additional features and services. Instead of implementing a simple and reliable identity credential, programmes are often expanded to include digital wallets, benefits integration, authentication frameworks, and multiple service layers. While these features may appear attractive from a policy perspective, they significantly increase system complexity and the risk of implementation failure.
International examples suggest a different approach. Countries such as Germany and France have implemented relatively straightforward identity systems that focus primarily on providing a reliable identity credential. Additional services can then be layered on top of this infrastructure over time, rather than being embedded into the initial design.
In practice, successful identity infrastructure often depends less on ambitious feature sets and more on disciplined engineering: clearly defined scope, strong security design, and incremental implementation.
The lessons from earlier identity programmes are directly relevant to the current wave of age-verification and digital identity proposals. If identity attributes are increasingly becoming part of the architecture of online systems, then the quality of the underlying identity infrastructure will matter enormously. Poorly designed systems risk creating fragile or intrusive identity mechanisms, while well-designed systems could provide narrowly scoped credentials, such as age verification, without exposing unnecessary personal data. In this sense, the debate about digital identity is not simply about whether identity systems should exist, but about how carefully they are engineered and how narrowly their scope is defined.
Government digital infrastructure has also faced criticism from oversight bodies. Reports from the UK National Audit Office have highlighted systemic cybersecurity risks and weaknesses in how data is shared across government systems, illustrating the institutional challenges involved in building large-scale digital infrastructure.
4.8 The European Contrast: France and Germany
The UK’s reluctance to adopt identity cards stands in contrast to many European countries.
In France, national identity cards have existed for decades and are widely accepted administrative tools. French citizens routinely use them for identification, travel within the European Union, and access to public services.
Similarly, Germany operates a national identity card system that includes digital identity functionality. The German electronic identity card allows citizens to authenticate themselves online for government and commercial services.
In these countries identity cards are largely viewed as administrative infrastructure rather than instruments of surveillance.
4.8.1 UK–France–Germany Identity Infrastructure Comparison Table
| Country | National ID Card | Population Registry | Digital Identity Integration | Public Perception |
|---|---|---|---|---|
| United Kingdom | No permanent national ID card (wartime cards abolished in 1952; 2006 ID scheme repealed in 2010) | No comprehensive population registry | Fragmented systems (Government Gateway, GOV.UK Verify, One Login) | Politically contentious; identity systems often framed as civil liberties issues |
| France | Long-standing national identity card (Carte Nationale d’Identité) | Centralised administrative records | Increasing integration with digital government services | Widely accepted as normal administrative infrastructure |
| Germany | Mandatory national identity card (Personalausweis) | Comprehensive municipal population registry (Melderegister) | Built-in electronic identity functionality for online authentication | Accepted as routine state infrastructure |
| Estonia (reference example) | Universal national digital ID | Fully integrated national registry | Extensive digital identity ecosystem for public and private services | Seen as core digital infrastructure |
Key point for readers:
- While many European states treat identity credentials as basic administrative infrastructure, the UK historically treats them as politically sensitive civil liberties questions.
4.9 Why the UK Debate Is Different
Several factors explain why identity systems are more controversial in the UK.
First, Britain lacks a tradition of national population registries common in many continental European states.
Second, the UK’s constitutional culture places strong emphasis on informal liberties and resistance to compulsory documentation.
Third, previous attempts to introduce identity systems have repeatedly collapsed, creating institutional memory and skepticism.
The result is a political environment in which identity infrastructure proposals are often interpreted through the lens of civil liberties debates rather than administrative efficiency.
4.10 From ID Cards to Digital Identity
Despite this historical resistance, identity systems are gradually re-emerging in new forms.
Modern digital identity proposals differ from earlier identity card schemes in several important ways:
- they often rely on distributed credentials rather than centralised databases
- they integrate with smartphones and online authentication systems
- they can support specific attributes, such as age verification, without revealing full identity.
These developments suggest that identity infrastructure may emerge incrementally rather than through a single national identity card programme.
In this sense, contemporary age verification systems may represent a partial reintroduction of identity mechanisms into the architecture of the internet.
4.11 And onto Age Verification
The long and contentious history of identity systems in the United Kingdom helps explain why contemporary debates about digital identity and age verification often become politically charged. Direct attempts to introduce comprehensive identity infrastructure (such as national ID cards or centralised digital identity systems) have repeatedly failed.
Yet identity attributes are now quietly reappearing through narrower regulatory mechanisms such as age verification and online safety laws. Rather than being introduced as a single national identity programme, identity credentials are emerging incrementally as functional components of digital systems. In this sense, the current wave of age verification may represent an indirect route toward forms of identity infrastructure that earlier political debates made difficult to introduce explicitly.
4.12 The Reality of Identity in the UK: De Facto Systems and Structural Gaps
Despite the UK’s historical resistance to national identity cards, identity infrastructure already exists in partial and fragmented forms. Several government identifiers function as de facto identity credentials, even if they were never designed as such.
One of the most prominent examples is the National Insurance number (NINO). Originally introduced to administer the social security system, the National Insurance number now serves as a widely used identifier across multiple areas of government interaction, including taxation, employment, and benefits administration. In practice, it functions as a quasi-identity number for many citizens.
However, the National Insurance system was not designed to operate as a universal identity credential. Not everyone possesses a permanent National Insurance number, temporary numbers exist for certain cases, and the system lacks the broader identity assurance features required for a modern identity infrastructure. These limitations illustrate the challenges of relying on systems that evolved for administrative purposes rather than being designed as identity platforms.
One possible alternative approach would be to build upon such existing identifiers rather than creating entirely new systems. Expanding an existing identifier into a properly designed digital identity credential could provide a simpler and more incremental path toward identity infrastructure than introducing a completely new national identity system.
At the same time, modern digital identity debates increasingly emphasise the importance of user control over identity data. Identity theorists such as Kim Cameron have articulated principles for identity systems that prioritise user autonomy and minimal disclosure. Cameron’s “Laws of Identity,” along with later developments such as Tim Berners-Lee’s work on Solid and personal data pods, propose identity architectures in which individuals retain control over their own credentials and personal data.
In such models, identity infrastructure does not mean centralised government ownership of personal information. Instead, individuals hold credentials that can be selectively presented to services when required. This approach aims to balance the administrative benefits of identity systems with stronger protections for privacy and personal autonomy.
Operational experience also highlights another dimension of the identity debate. During work on border control systems in the UK, conversations with enforcement teams and individuals encountered during border operations revealed a recurring observation: the relative fragmentation of identity management across UK institutions can make it easier for individuals to navigate between different systems without consistent identity verification.
In contrast, countries with more integrated identity infrastructures, such as France and Germany, often link government services more closely to verified identity credentials. While this does not eliminate irregular migration or identity fraud, it changes the structure of the administrative environment in which individuals operate.
These observations illustrate a broader point: the debate over identity systems in the UK is not simply about whether identity infrastructure should exist. In practice, identity mechanisms already exist in partial forms across different systems. The real policy question is how those mechanisms should be designed, governed, and integrated in ways that balance administrative effectiveness, security, and individual autonomy.
In effect, the National Insurance number already functions as a persistent identity attribute within parts of the UK administrative system: an early example of the kind of identity-linked infrastructure that is now beginning to appear more broadly across digital platforms.
Oversight reports have repeatedly highlighted the fragmentation of data systems across UK government departments. A National Audit Office review of cross-government data use noted significant challenges in linking and sharing identity information between agencies, reflecting the absence of a unified identity infrastructure.
And so, in this sense, the age-verification wave may represent not a departure from the UK’s long struggle over identity infrastructure, but its latest and more indirect iteration. Today, identity attributes are increasingly embedded invisibly within the infrastructure of digital platforms.
5. What People Think Is Happening
Whenever a technological system begins to change its underlying architecture, public understanding tends to organise itself around narratives. These narratives are rarely entirely wrong, but they are often incomplete. They simplify a complex transition into a story that can be easily communicated, debated, and politically mobilised.
The emerging age-verification regime is no exception. Across policy debates, media coverage, and online discourse, two dominant interpretations have crystallised. Each reflects a particular set of concerns, and each draws on real developments within the legislative landscape described in the previous section. Yet neither fully captures the structural transformation that is underway.
To understand what is actually happening, it is useful to examine these two narratives in turn.
5.1 Narrative A: Child Protection
The first narrative is the official one. Governments introducing age-verification laws almost invariably frame them as necessary interventions to protect children from a digital environment that has become increasingly difficult to regulate through traditional means.
Over the past decade, concerns about youth wellbeing online have intensified. Policymakers point to a range of issues that appear to correlate with the expansion of social media platforms and algorithmically curated digital spaces. Within this framing, age verification is not a mechanism of control but a tool for safeguarding vulnerable users.
The arguments generally revolve around several related claims:
- Protecting children from harmful content. Legislators frequently cite the ease with which minors can encounter pornography, self-harm material, or other forms of disturbing content online.
- Reducing social media addiction. A growing body of research suggests that algorithmic feeds may encourage compulsive engagement patterns, particularly among adolescents.
- Preventing grooming and exploitation. Law enforcement agencies have raised concerns about adults using online platforms to target minors.
- Addressing youth mental health challenges. Rising levels of anxiety, depression, and self-harm among teenagers are often linked, sometimes controversially, to social media exposure.
Within this narrative, the regulatory logic appears straightforward. If platforms are required to protect children from certain types of content or interaction, they must first be able to identify which users are children. Age verification, therefore, becomes a technical prerequisite for enforcing child-safety rules.
From this perspective, the emerging regulatory architecture is not fundamentally about controlling the internet but about adapting existing child protection principles to a digital environment where traditional safeguards have failed.
To many policymakers, the absence of reliable age verification online appears anomalous. In the physical world, access to restricted goods or environments, alcohol, and gambling venues, all adult entertainment already depend on some form of age verification. Extending similar safeguards to the internet seems, in this view, both logical and overdue.
Yet the simplicity of this reasoning also conceals important complexities.
5.2 Narrative B: The “Censorship Industrial Complex”
Opposition to age-verification laws has produced a very different narrative, particularly among civil liberties advocates, technologists, and segments of the online policy community.
Within this framework, age verification is not merely a child protection mechanism but the leading edge of a broader system of digital control. Critics argue that once governments or platforms possess the technical ability to verify user identity attributes, that capability can be extended to regulate speech, participation, and access to information.
This interpretation frequently invokes what some commentators describe as a “censorship industrial complex”, a network of governmental institutions, regulatory bodies, and platform governance mechanisms capable of shaping online discourse at scale.
The concerns associated with this narrative typically fall into three categories:
- The erosion of anonymity. Mandatory age verification could require users to provide personal information, identity documents, biometric data, or financial credentials before accessing online services. Critics argue that such systems fundamentally undermine the anonymous or pseudonymous participation that has historically characterised the internet.
- Expanded mechanisms of speech control. Once identity attributes are integrated into platform infrastructure, regulators may gain the ability to enforce differentiated rules for different categories of users. Age verification could thus become a gateway to broader systems of speech governance.
- Concentration of power. Implementing large-scale verification systems tends to favour major technology companies capable of absorbing compliance costs, potentially reinforcing the dominance of existing platforms.
For critics operating within this framework, the trajectory appears clear. Age verification begins with child safety, but it establishes a technical infrastructure that could support far more expansive forms of digital governance.
The argument is not that every policymaker intends such an outcome. Rather, it is that the underlying architecture of identity verification creates possibilities that extend well beyond the original regulatory rationale.
5.3 Narrative C: Advertising Markets and Bot Detection
A third narrative emerging in online discussions attributes the push toward identity verification to pressures within digital advertising markets.
Advertising systems depend heavily on measuring human attention. As automated content generation and bot traffic increase, distinguishing genuine human engagement from automated activity becomes more difficult. Advertisers increasingly demand assurance that the audiences they pay to reach represent real people rather than automated systems or engagement farms.
From this perspective, stronger identity signals could help platforms demonstrate the authenticity of their user base. Age or identity attributes would function as signals of human users, improving confidence in advertising metrics.
While this explanation does not appear to be the primary driver of recent legislation, it reflects a broader economic pressure within digital platforms: the need to maintain trust in the authenticity of online audiences.
5.4 Narrative D: Platforms Shifting Verification to Infrastructure
A fourth narrative focuses on the strategic incentives of large platforms.
Rather than verifying user identity directly within their own services, platforms increasingly advocate for age verification to occur at deeper layers of the digital ecosystem, such as operating systems or device-level services.
Under this model, identity attributes are verified once at the device or account level and then made available to applications through standardised interfaces. Platforms can then apply age-based rules without storing sensitive identity data themselves.
This approach reduces liability and operational complexity for individual platforms while embedding identity signals into shared digital infrastructure.
As a result, policy debates about age verification increasingly intersect with operating system providers, app stores, and device manufacturers rather than only with individual online services.
5.5 The Limits of These Narratives
Each of these interpretations captures a genuine dimension of the current policy debate. Governments are indeed motivated by concerns about child safety and youth wellbeing. At the same time, critics are correct that large-scale identity infrastructure introduces new capacities for monitoring and controlling digital participation.
Yet taken individually, both narratives obscure the deeper transformation now underway.
The child protection narrative focuses primarily on the policy justification for age verification. The censorship narrative focuses on its potential consequences. What neither fully addresses is the structural shift in how digital environments themselves are being organised.
At its core, the emerging system is less about removing particular pieces of content than about classifying users before interaction occurs. The architecture being built does not merely regulate information; it determines which categories of users may access which types of digital spaces in the first place.
In other words, the internet is gradually moving from a model in which:
- users enter a largely open network and content is moderated afterward
toward one in which:
- user attributes are determined first, and the platform environment is configured accordingly.
This shift is subtle, but it is significant. It marks a transition from content-based governance toward identity-mediated governance.
Understanding that transition requires looking not only at the policies themselves but also at the technological systems being constructed to implement them.
Although these narratives differ in their explanations, they converge on a similar structural outcome.
Whether driven by child safety concerns, regulatory pressure, advertising economics, or platform strategy, many proposals ultimately require systems capable of verifying and transmitting identity attributes across digital services.
This convergence suggests that the most significant transformation may not lie in the motivations behind age verification but in the architectural changes required to implement it.
5.6 Emerging Policy Debate
Public discussion surrounding age-verification laws has intensified as the first wave of policies begins to move from legislation to implementation.
Government regulators and child-safety advocates increasingly frame age verification as a necessary adaptation to a digital environment in which children encounter content and interactions that earlier regulatory frameworks were not designed to address. Several jurisdictions have begun enforcing social media age restrictions or platform safety obligations, and technology companies have responded by developing new technical tools such as operating-system age APIs, platform-level verification systems, and third-party identity services.
At the same time, privacy advocates, digital-rights organisations, and some researchers have raised concerns about the broader implications of these systems. Critics warn that large-scale age verification could introduce new forms of identity infrastructure into the architecture of the internet, potentially enabling expanded monitoring of online participation and reducing the range of spaces in which users can interact anonymously.
These debates often focus on the immediate effectiveness or risks of particular age-verification systems. Yet the deeper significance of the current moment may lie less in any single implementation and more in the structural trajectory that is beginning to emerge. Across different jurisdictions and technological ecosystems, similar patterns are appearing: regulatory pressure creates incentives to classify users, platforms seek scalable verification mechanisms, and identity attributes become embedded within technical infrastructure.
Understanding the long-term consequences of these developments therefore requires looking beyond the immediate policy controversy toward the architectural transformations they may produce.
5.7 Moderation vs. Environment Design
Seen from this perspective, the most important change is conceptual rather than technical.
The earlier internet treated harmful content primarily as a problem of moderation. The emerging model treats it as a problem of environment design.
Moderation removes or labels specific pieces of information after they appear. Environment design determines what information becomes visible to particular users in the first place.
The difference is subtle but profound. Moderation operates at the level of individual posts. Environment design operates at the level of the system itself.
Age verification, in this sense, is not simply a compliance mechanism. It is the key that allows platforms and regulators to begin reorganising the structure of the digital environment around categories of users.
And once that key exists, the architecture of the internet begins to change.
5.8 A Historical Precedent: Governance Migration in Telecommunications
The migration of governance toward deeper layers of digital infrastructure is not unprecedented.
During the development of modern telecommunications networks in the late twentieth century, regulators initially attempted to control specific services and applications operating on top of telephone networks. Over time, however, it became clear that regulating individual services was impractical as the number of services expanded.
Regulatory frameworks gradually shifted toward the infrastructure layer of telecommunications networks. Obligations were imposed on network operators to support capabilities such as lawful interception, emergency call routing, and number portability. By regulating the infrastructure through which services operated, policymakers could influence the entire communications ecosystem rather than attempting to regulate each service individually.
The current evolution of age verification policy may represent a similar shift. Rather than imposing requirements on individual websites or applications, policymakers are increasingly exploring mechanisms that operate at deeper layers of the digital stack, including operating systems and device-level services.
5.9 Motivations and Structural Outcomes
Public debates about age verification often focus on identifying the primary motivation behind these policies. Some observers emphasise child safety concerns, while others highlight regulatory pressure, platform liability, advertising economics, or strategic positioning by large technology companies.
These explanations may all capture part of the broader landscape.
However, the motivations behind policy proposals are often difficult to determine with certainty and may vary across jurisdictions and actors. Policymakers, companies, advocacy groups, and regulators frequently pursue different objectives simultaneously.
For this reason, the present analysis focuses less on determining the precise motivations behind age verification initiatives and more on examining the structural consequences of the mechanisms being proposed.
Regardless of the motivations driving these policies, implementing age verification at scale requires systems capable of reliably classifying users and communicating those classifications across digital services.
This requirement introduces new forms of identity infrastructure into the technical architecture of the internet.
The central question, therefore, is not only why these policies are being proposed, but also how the mechanisms used to implement them may reshape the structure of digital environments.
6. What Is Actually Being Built
The previous sections described two things: the laws that are emerging across jurisdictions, and the public narratives through which those laws are interpreted. Both are important, but neither fully explains the deeper transformation underway. To understand the significance of the current policy wave, it is necessary to step back from the legislation itself and examine the architecture of the internet systems these laws are gradually forcing into existence.
At its most fundamental level, the shift can be summarised in a single transition.
For most of the modern internet, governance occurred after information was published. Content appeared first; moderation happened later.
In simplified form, the old model looked something like this:
content → moderation
A user could create an account, often pseudonymously, and publish text, images, or video. Platforms might subsequently review the material, remove it, label it, or demote its visibility according to their policies. But the governing principle was reactive. The system intervened after content entered circulation.
The emerging architecture reverses this sequence.
Instead of waiting for content to appear and then deciding how to respond, the new model begins by determining who the user is, or more precisely, what category of user they belong to. Only once that classification has occurred does the system decide what content, features, or algorithmic pathways will be available.
The resulting logic looks like this:
identity → rules → algorithmic exposure
The distinction may appear subtle, but its consequences are significant. Under this architecture, the user’s attributes (age, identity status, or other credentials) shape the digital environment before interaction even begins.
As illustrated in Figure 1, “Evolution of Internet Architecture (1990–2035)”, governance is gradually shifting downward from platforms toward identity infrastructure and operating-system layers.
In this sense, the emerging system does not simply moderate content. It configures information environments.
6.1 The Downward Migration of Internet Governance
A recurring pattern in the history of internet governance is that regulatory authority gradually migrates downward through the technical stack.
In the early years of the web, governance occurred primarily at the level of individual websites and communities. Moderation decisions were made locally by site operators or administrators. As digital platforms grew in scale, governance shifted toward the platform layer. Large social networks and content platforms began establishing global rules governing speech, behaviour, and content visibility.
Over time, however, regulators and policymakers discovered that enforcement at the level of individual platforms remained difficult. Platforms could relocate across jurisdictions, challenge regulations in court, or modify their systems in ways that complicated oversight.
As a result, regulatory pressure increasingly moved toward deeper layers of the technological infrastructure.
This migration can be understood as a sequence:
content layer
↓
platform layer
↓
infrastructure layer
Examples of this pattern appear throughout the history of internet governance. Copyright enforcement gradually expanded from content takedowns toward obligations imposed on hosting providers and internet service providers. Financial regulation increasingly relies on payment processors to enforce restrictions on digital transactions. Domain name registries and DNS infrastructure have also become points of policy intervention in areas ranging from intellectual property to national security.
The current wave of age-verification policy appears to follow the same trajectory.
Early attempts to enforce age restrictions focused on individual websites, particularly adult content platforms. These efforts proved difficult to implement at scale. Policymakers therefore began shifting enforcement toward larger intermediaries such as social media platforms.
More recently, regulatory attention has begun moving even deeper into the technology stack, targeting operating systems and application distribution channels as enforcement points.
This progression reflects a broader principle of digital governance:
the deeper a regulatory control point sits within the technical architecture of the internet, the more difficult it becomes for services to bypass.
Age verification illustrates this pattern clearly. What began as a proposal aimed at specific categories of websites is gradually evolving into identity infrastructure embedded within operating systems and platform ecosystems.
6.2 The Old Internet
To understand the scale of this change, it is helpful to briefly revisit how the web historically functioned.
The early internet was built around a relatively simple interaction model:
anonymous users
↓
websites
↓
content moderation
A visitor arrived at a site, forum, or platform and participated under a username that might or might not correspond to a real-world identity. Platforms moderated behaviour through a mixture of community rules, automated filtering, and human review. Content deemed illegal or harmful could be removed, but the system itself rarely required prior verification of the user.
This architecture emerged partly from technical constraints and partly from the cultural ethos of the early internet. Openness and pseudonymity were not merely tolerated but often celebrated as enabling features of a global communication network.
Even as large social platforms grew to dominate online interaction in the 2010s, the basic model remained intact. Users might create accounts tied to email addresses or phone numbers, but the system did not fundamentally depend on verifying who the user was before allowing participation.
Moderation was an overlay applied to an otherwise open network.
6.3 The Emerging Internet
The regulatory initiatives discussed earlier are gradually introducing a different organisational logic.
Instead of beginning with anonymous access, the system increasingly begins with identity attributes. These attributes do not necessarily reveal a user’s full identity; in many cases they consist only of categorical information such as whether the user is a minor or an adult. Yet even this limited classification allows platforms to structure the environment differently for different groups of users.
The architecture now being assembled resembles something closer to the following model:
identity attributes
↓
platform governance
↓
algorithmic environments
The sequence matters.
First, the system determines the relevant attributes of the user, most commonly age, but potentially others in the future. Next, platform governance rules interpret those attributes and determine which regulatory obligations apply. Finally, algorithmic systems use those rules to shape the user’s informational environment: which content appears, which features are available, and which interactions are permitted.
What results is not merely moderation but differentiated information ecosystems.
A minor user might encounter stricter content filters, limited messaging capabilities, and altered recommendation algorithms. An adult user might see a broader range of material and possess additional interaction privileges. In both cases, the platform is not simply removing specific posts; it is constructing an environment tailored to the regulatory category assigned to the user.
6.4 Identity as Infrastructure
Age verification, therefore, represents more than a technical compliance mechanism. It is the first large-scale deployment of identity attributes as infrastructure for governing digital platforms.
Once the system is capable of determining whether a user is under thirteen, under sixteen, or over eighteen, it becomes possible to apply a wide variety of platform rules based on that classification. Recommendation systems can be tuned differently. Messaging systems can impose different constraints. Certain types of content can be excluded entirely from one user category while remaining available to another.
The architecture is inherently extensible. Age may be the first attribute regulators require, but it is unlikely to be the last.
Indeed, the logic underlying these systems could easily accommodate other attributes in the future:
- verified identity status
- citizenship or jurisdiction
- parental consent credentials
- professional or educational qualifications.
Whether such extensions ultimately occur remains uncertain. What is clear is that the technological infrastructure being developed to support age verification is capable of supporting far broader systems of classification.
6.5 Diverging Architectural Directions
As identity attributes begin to appear within internet infrastructure, two broad architectural directions are emerging.
6.5.1 Path A: Platform-Centric
In this model, identity signals are primarily used to support governance and optimisation within digital platforms.
Identity attributes enable systems to classify users before interaction occurs and apply rules accordingly.
Typical uses include:
- regulatory compliance (such as age restrictions)
- platform governance and moderation
- algorithmic optimisation and behavioural classification
Identity becomes an input into the operational logic of digital environments.
6.5.2 Path B: Citizen-Centric
In this alternative model, identity credentials are designed to reduce data collection and place individuals at the centre of digital interactions.
Rather than services acquiring and storing personal data, users present verifiable credentials that prove specific attributes when required.
Typical uses include:
- proving eligibility for services
- reducing unnecessary data disclosure
- decentralised verification of personal attributes
Both paths rely on similar technological components, yet they imply very different trajectories for the architecture of the internet.
6.6 Competing Models of Identity Infrastructure
As identity attributes begin to appear within the technical infrastructure of digital systems, an important architectural tension becomes visible.
Two distinct models of identity infrastructure are emerging.
The first can be described as regulatory identity. In this model, identity attributes exist primarily to enable governance and enforcement within digital platforms. Systems such as age verification classify users according to regulatory categories, allowing platforms to apply rules before interaction occurs. These identity signals support mechanisms such as age restrictions, platform governance frameworks, and algorithmic moderation systems.
The second model can be described as sovereign or citizen-centric identity. Here, the objective is not to enable platform control but to minimise data collection and place individuals at the centre of digital interactions. Instead of services collecting and storing personal data repeatedly, users present verifiable credentials that prove specific attributes when required.
In such systems, the emphasis is on proof rather than disclosure. A user might demonstrate that they are “over 21” or “eligible for a service” without revealing their full identity or underlying personal data.
Both models rely on the same underlying technical foundations: cryptographic credentials and verifiable attribute systems. Yet they point toward very different architectural outcomes.
In the regulatory model, identity attributes become inputs to governance systems that structure access to digital environments. In the citizen-centric model, identity credentials function as tools that allow individuals to interact with services while retaining control over their personal data.
The distinction is subtle but significant. The same technological mechanisms, verifiable credentials, digital identity wallets, and attribute proofs, can support either architecture depending on how they are deployed.
Within the identity research community, this distinction is often illustrated through simple examples. Rather than distributing full identity information such as date of birth, systems may instead allow a user to present a cryptographic proof of a specific attribute, for example, confirming that the individual is “over 21”.
From a privacy perspective, this approach reduces the amount of personal data that must be shared between systems. From a regulatory perspective, however, the same capability provides a mechanism through which platforms and infrastructure providers can classify users before interaction occurs.
The result is an emerging duality.
One trajectory emphasises identity as a tool for individual autonomy and minimal disclosure.
The other emphasises identity as a mechanism for structuring and governing digital environments.
Both trajectories are developing simultaneously within the same technological ecosystem. The infrastructure now being built for age verification and online safety regulation therefore sits at the intersection of these two models.
Which architecture ultimately dominates may depend less on the technology itself than on the governance structures surrounding it.
These architectural directions correspond to two distinct models of identity infrastructure.
6.6.1 Model 1: Regulatory Identity
In the regulatory model, identity attributes exist primarily to enable enforcement within digital systems.
They allow platforms and infrastructure providers to apply rules before interaction occurs.
Common uses include:
- enforcing age restrictions
- implementing platform governance frameworks
- supporting behavioural classification within algorithmic systems
Identity functions as a tool of digital regulation.
6.6.2 Model 2: Sovereign Identity
In the sovereign or citizen-centric model, identity credentials exist to empower individuals and minimise data collection.
Instead of services collecting and storing personal data repeatedly, users present verifiable credentials that demonstrate specific attributes when required.
Typical characteristics include:
- minimal disclosure of personal information
- user-controlled credentials
- proof of eligibility without revealing underlying data
Both models rely on the same underlying technical mechanisms, particularly verifiable credentials and cryptographic attribute proofs, yet they lead to very different internet architectures.
6.7 Attribute Proof Rather Than Disclosure
Within the digital identity community, a common illustration of privacy-preserving identity systems is the idea that a user should be able to prove that they are “over 21” without revealing their full date of birth.
In such systems, a cryptographic credential confirms the required attribute while preventing unnecessary disclosure of personal data.
From a privacy perspective, this approach reduces the amount of personal information shared between services.
From a regulatory perspective, however, the same mechanism provides a way for platforms and infrastructure providers to classify users before interaction occurs.
The technology is identical.
What differs is the motivation.
Where identity researchers often see privacy-preserving attribute credentials, regulators frequently see age-verification infrastructure.
The same technical foundation therefore supports two very different interpretations of digital identity.
6.8 The Internet’s Anti-Identity Origins
Many of the technologies that shaped the early internet emerged from military and academic research environments. Systems such as ARPANET were designed to be resilient, decentralised, and capable of functioning even if parts of the network were disrupted. The emphasis was on routing information reliably across distributed systems, not on verifying the identity of the individuals using them.
This architectural philosophy had important consequences. Internet protocols were designed primarily to move packets of information rather than to authenticate people. As a result, anonymity and pseudonymity became natural properties of the network. Users could communicate, publish information, or participate in online communities without necessarily revealing who they were.
For many years this characteristic was widely seen as one of the internet’s defining freedoms. It enabled whistleblowers, activists, and ordinary individuals to speak without fear of retaliation. At the same time, the absence of strong identity mechanisms also created space for harassment, fraud, and abuse.
Advocates addressing online harms have increasingly pointed out this tension. As digital rights advocate Nina Jane Patel has argued following her experiences of abuse in immersive online environments, anonymity can also enable harmful behaviour that is difficult to prevent or punish.
The current wave of identity infrastructure, age verification, digital identity credentials, and platform governance systems, can therefore be understood as a partial reversal of the internet’s original design philosophy. Where early internet architecture treated identity as largely irrelevant to network operation, modern regulatory frameworks increasingly treat identity as central to how digital systems are governed.
6.9 Environment Design
A key conceptual shift underlying the current regulatory transformation is the move from moderation to environment design.
For most of the internet’s history, governance occurred primarily through moderation mechanisms that responded to content after it had been published. Platforms removed harmful posts, banned users who violated rules, or labelled certain types of information.
The emerging model operates differently.
Rather than focusing exclusively on removing harmful content after the fact, platforms increasingly design digital environments that limit which types of content become visible to particular categories of users in the first place.
This approach can be described as environment design.
Environment design operates at a different level than moderation. Instead of regulating individual pieces of information, it structures the conditions under which users encounter information at all.
Identity attributes are central to this process. Once platforms can determine whether a user is a child, teenager, or adult, they can configure the environment differently for each group. Recommendation systems, messaging permissions, content filters, and interaction features can all be adjusted according to the user’s classification.
The result is not simply the removal of specific posts or videos but the construction of differentiated informational ecosystems.
Age verification, therefore, functions not only as a compliance mechanism but also as a key enabling component of environment design.
6.10 Evaluating the Emerging Identity-Mediated Internet as Digital Public Infrastructure (DPI)
The emergence of age-verification infrastructure can also be understood through the policy lens of Digital Public Infrastructure (DPI). DPI frameworks typically identify three foundational capabilities for participation in digital society: authentication (identity), transactions (payments), and data exchange across institutions. Age verification systems represent a specialised form of authentication infrastructure embedded within the operational stack of the internet. Once deployed at scale, such systems introduce persistent identity attributes into digital environments, enabling platforms to classify users before interaction occurs. This raises a critical question for policymakers: whether the identity infrastructure emerging through age-verification mandates satisfies the core attributes expected of DPI, including interoperability, privacy protection, transparency, and inclusion.
DPI frameworks commonly evaluate infrastructure according to six attributes that determine whether digital systems function as public infrastructure rather than fragmented technical solutions.
Interoperability and extensibility
Identity attributes must function across platforms, devices, and jurisdictions if they are to operate as shared infrastructure. Age credentials stored in operating systems or digital identity wallets will likely need to interoperate between governments, technology providers, and online services.
Transparency, accountability, and oversight
DPI systems typically require governance structures ensuring that infrastructure operators can be held accountable. When identity verification moves into operating systems and platform ecosystems, governance authority may shift from public institutions toward private infrastructure providers.
Privacy, safety, and security
Age verification requires processing sensitive personal information. The architectural design of identity infrastructure determines whether verification can occur without exposing unnecessary personal data.
Inclusion and non-discrimination
Identity systems risk excluding users who lack government identification, compatible devices, or access to digital credential systems.
Capacity and coordination
Implementing identity infrastructure requires coordination across governments, identity providers, device manufacturers, and platforms.
Scale of adoption
Infrastructure becomes truly infrastructural when it is used widely across many services and institutions. Age verification embedded within operating systems could quickly reach global scale.
7. How OS-Level Age Verification APIs Work
If age verification is the regulatory objective, the immediate technical question becomes obvious: where should the verification occur?
The earliest proposals, those discussed in the mid-2010s, assumed that individual websites would implement their own age checks. A pornography site might require a credit card, a social network might ask for a birth date, and a gaming service might request parental consent. Each service would enforce its own verification scheme independently.
That model proved difficult to enforce at scale. Websites exist across jurisdictions, and compliance could be evaded simply by visiting a non-compliant service or misreporting one’s age. As policymakers and platforms confronted these limitations, a different idea began to emerge: rather than verifying age at the application layer, verification could occur deeper in the software stack.
In practical terms, this means pushing age verification down into the operating system itself.
Modern computing platforms, whether smartphones, desktops, or gaming consoles, already rely on operating systems to manage identity-related functions. Apple IDs, Google accounts, and Microsoft accounts serve as foundational identity anchors for the devices on which users run applications. These systems already store credentials, manage permissions, and enforce security policies.
Age verification systems can therefore be built on top of this existing identity infrastructure.
7.1 The Basic Process
An operating-system-level verification model generally follows a relatively simple sequence.
First, the user provides a date of birth during account creation or device setup. Most modern operating systems already collect this information as part of their standard onboarding process.
Second, the operating system translates that date of birth into an age classification. Rather than exposing the exact birth date to applications, the system converts it into a category relevant to regulatory requirements.
Third, that age category is stored within the operating system’s secure credential infrastructure.
Finally, applications that need to enforce age restrictions can query the operating system through a standardised interface, an API, to determine the user’s age category.
In simplified form, the process looks like this:
- The user enters a date of birth during account setup.
- The operating system calculates the user’s age bracket.
- The age classification is stored in a secure credential store.
- Applications query the operating system to determine the age category.
This approach allows the operating system to act as a trusted intermediary between regulators, platforms, and users.
7.2 Age Credentials
In practice, operating systems would not expose raw personal data such as a birth date to applications. Instead, they would generate a credential describing the user’s age category.
A simplified example might look like the following:
credential {
attribute: age_class
value: minor_13_15
}
In this structure the operating system stores only the attribute required for regulatory enforcement. The application learns that the user belongs to a specific age bracket but does not gain access to the underlying birth date or other identifying information.
From a privacy perspective, this distinction matters. The system reveals just enough information for the application to enforce platform rules while avoiding the unnecessary distribution of personal data.
7.3 The Age Verification API
Applications interact with this credential through an operating system interface, an Age Verification API.
Instead of collecting age information themselves, applications simply request the relevant classification from the operating system.
A simplified API call might look something like this:
AgeAPI.getAgeClass()
The system would return a response indicating the user’s category:
adult
teen
child
The application can then use this classification to determine how its features should behave. Certain content might be restricted for minors. Messaging capabilities might be limited. Recommendation algorithms might operate under different rules.
Crucially, the application never handles the underlying personal data directly. The operating system mediates the exchange.
7.4 Why the Operating System Layer Matters
From a regulatory perspective, the operating system occupies a uniquely powerful position in the technology stack.
Unlike individual websites, operating systems control the environment in which applications execute. They already manage permissions for access to hardware, sensors, filesystems, and networks. Adding an age classification service to this layer therefore aligns with an existing security model.
It also solves several problems that earlier verification schemes struggled with:
- Consistency. Applications receive age information from a standardised source rather than implementing incompatible verification systems.
- Reduced duplication. Users verify their age once rather than repeatedly across different services.
- Platform enforcement. App stores can require applications to respect the age signals provided by the operating system.
For regulators, this architecture has an additional advantage. Operating systems are controlled by a relatively small number of companies, primarily Apple, Google, and Microsoft. Implementing age verification at this level concentrates enforcement on a handful of entities rather than thousands of independent websites.
7.5 OS Age Verification Architecture
The resulting system can be visualised as a layered structure.
user
↓
identity provider
↓
OS credential store
↓
age API
↓
applications request age status
At the top sits the user and whatever identity provider verifies their credentials. Beneath that lies the operating system’s secure storage environment, where age classifications are maintained. Applications interact with the system through a controlled interface rather than accessing personal information directly.
In effect, the operating system becomes the authority that certifies a user’s age category to applications running on the device.
7.6 The Significance of the Shift
From a purely technical perspective, the architecture is elegant. It centralises verification, reduces data duplication, and integrates with existing device identity systems. From a regulatory perspective, it is attractive because it concentrates enforcement at a small number of infrastructure providers.
Yet the implications extend beyond convenience.
Once age verification is embedded within the operating system layer, identity attributes become part of the fundamental infrastructure of digital interaction. Applications no longer operate within a neutral environment in which users arrive anonymously. Instead, they operate within an ecosystem where the platform already knows certain characteristics about the user before the application even begins.
Age verification is, therefore, not merely a feature added to the operating system. It is a step toward integrating identity attributes directly into the underlying fabric of digital platforms.
And once those attributes exist, they inevitably become available to shape the environments that users inhabit.
7.7 Limitations of First-Generation Systems
Many currently deployed age-verification systems remain relatively easy to circumvent. Users frequently report bypassing restrictions through methods such as virtual private networks (VPNs), borrowing identification from older individuals, or exploiting weaknesses in automated facial age-estimation systems. In some cases, simple behavioural workarounds allow users to continue accessing services despite formal restrictions.
These limitations are not unusual for the early stages of regulatory technologies. Initial implementations often emerge rapidly in response to legislative pressure and operate within incomplete technical ecosystems.
Over time, however, regulatory infrastructures tend to evolve. Institutional incentives encourage platforms, regulators, and technology providers to close gaps, improve verification mechanisms, and integrate systems more tightly across services and devices.
In this sense, the current generation of age-verification technologies can be understood as an early phase in a longer process of infrastructure development. The systems being deployed today may be imperfect, but they establish the architectural foundations upon which more integrated identity-verification mechanisms may later be constructed.
8. Why Governments Target Operating Systems
If the regulatory objective is to enforce age-based restrictions across large portions of the internet, the next question becomes one of engineering rather than law: where, precisely, can such rules be enforced?
This shift toward operating-system-level enforcement reflects the broader migration of governance into the infrastructure layer of the internet.
Operating systems occupy a uniquely powerful position within the digital ecosystem. They control device authentication, manage credential storage, and regulate how applications access hardware and system services. Because most digital services are accessed through a relatively small number of operating systems, primarily iOS, Android, Windows, and macOS, these platforms function as natural enforcement chokepoints.
For regulators seeking to implement age-verification rules across thousands of independent applications, the operating system layer offers a far more tractable point of intervention than the application layer itself.
If identity attributes are verified and stored at the operating-system level, applications can query those attributes through standardised interfaces. Compliance therefore becomes embedded within the infrastructure of the platform ecosystem rather than implemented separately by each individual service.
In this sense, operating systems are evolving from neutral technical environments into regulatory intermediaries that mediate how identity attributes are communicated across digital services.
Early attempts at age verification assumed that the responsibility would lie with individual websites. In theory, a platform could simply require users to verify their age before accessing restricted services. In practice, however, the internet does not behave like a neatly bounded regulatory domain. Websites can be hosted in different jurisdictions, accessed through alternative browsers, mirrored across servers, or replaced by new services that simply ignore the rules.
For regulators, this creates a familiar problem. Enforcement at the level of individual websites resembles trying to control traffic by regulating every vehicle independently rather than managing the road network itself.
Over the past decade policymakers have increasingly recognised that the modern internet is no longer organised primarily around independent websites. Instead, most digital activity now flows through a relatively small number of infrastructural layers that sit between the user and the services they access.
These layers form what might be described as the operational stack of contemporary internet usage:
device
↓
operating system
↓
app store
↓
platform
Each layer performs a different function, but together they form the pathway through which most users encounter digital services. Crucially, each layer is controlled by a limited number of actors.
This reflects the broader architectural shift outlined earlier in Figure 1, “Evolution of Internet Architecture (1990–2035)”, where regulatory obligations propagate through identity credentials and platform infrastructure.
For regulators attempting to enforce age verification rules, these layers function as regulatory choke points, locations within the technological architecture where compliance can be imposed effectively.
8.1 The Device Layer
At the base of the stack sits the user’s device: a smartphone, tablet, laptop, or gaming console. The device provides the physical interface through which the user interacts with the digital world.
Historically, regulators rarely targeted this layer directly. Hardware manufacturers were not responsible for policing online behaviour; that responsibility was left to service providers. However, as age verification systems increasingly integrate with device identity systems, the boundary between hardware and platform governance has begun to blur.
Even so, enforcement at the device level remains difficult. Hardware circulates globally, and once purchased it can operate in many regulatory environments.
The next layer is far more tractable.
8.2 The Operating System
Operating systems, iOS, Android, Windows, macOS, and others, control the environment in which applications run. They manage permissions, security policies, user identities, and access to device resources.
From a regulatory perspective, this layer is extraordinarily powerful.
Operating systems already perform many functions that resemble governance:
- they determine which applications can run on the device
- they control access to cameras, microphones, and location data
- they enforce security policies and cryptographic authentication.
Introducing an age classification system into this layer therefore represents a relatively natural extension of existing responsibilities.
More importantly, the number of operating system providers is small. A handful of companies effectively control the global market:
- Apple, through iOS and macOS
- Google, through Android
- Microsoft, through Windows.
By targeting the operating system layer, regulators can influence the behaviour of millions of applications simultaneously without interacting with each one individually.
Elements of this architecture are already beginning to appear in commercial operating systems and digital identity initiatives. Apple, for example, has introduced age-range signalling mechanisms within its platform ecosystem, allowing applications to request verified age category information without exposing full identity data. Google has explored similar approaches through Play Store age signals and account-level safety classifications.
At the policy level, the European Union’s emerging digital identity framework, including the European Digital Identity (EUDI) wallet, also includes provisions for age credentials that can be selectively disclosed to online services. These developments illustrate how age verification is gradually migrating into the infrastructure layer of digital ecosystems rather than remaining solely a feature implemented by individual applications.
8.3 The App Store Layer
Above the operating system sits another crucial control point: the application distribution system.
Most modern devices rely on centralised application stores, Apple’s App Store, Google Play, Microsoft Store, and similar platforms, to distribute software. These stores enforce technical and policy requirements before allowing applications onto the device.
For regulators, this creates a powerful enforcement mechanism. If age verification becomes a requirement for platform compliance, app stores can simply refuse to distribute applications that ignore the rule.
In other words, rather than forcing regulators to pursue thousands of individual developers, compliance can be enforced through the handful of companies that control software distribution.
8.4 The Platform Layer
Finally, the user interacts with digital platforms themselves: social networks, streaming services, gaming environments, messaging systems, and countless other applications.
These platforms ultimately determine how users interact with information and with each other. However, because platforms operate on top of operating systems and distribution channels controlled by others, they are not the most efficient point for regulatory enforcement.
Platforms can change their behaviour, relocate their servers, or challenge regulations in court. Infrastructure layers are harder to circumvent.
8.5 Internet Enforcement Chokepoints
When these layers are viewed together, the logic behind operating-system-level regulation becomes clear.
device
↓
operating system
↓
app store
↓
platform
The lower layers of the stack are more stable, more centralised, and more difficult for services to bypass. As a result, they provide far more reliable points for regulatory intervention.
This explains why age verification has gradually migrated from individual websites to platform infrastructure. Governments are not merely attempting to regulate content; they are attempting to regulate the architecture through which content is accessed.
8.6 Concentrated Power
This strategy has a further implication that is often overlooked. By targeting operating systems and distribution channels, regulators inevitably concentrate enforcement power within a small number of corporations.
Apple, Google, and Microsoft become not merely technology providers but gatekeepers of regulatory compliance. Their operating systems determine how identity attributes are stored and exposed to applications. Their app stores determine which services can reach users.
For policymakers, this concentration simplifies enforcement. For critics, it raises obvious questions about the relationship between private infrastructure providers and public regulation.
Either way, the trend is unmistakable. As digital governance moves deeper into the technological stack, the entities controlling that stack acquire an increasingly central role in how the internet itself is governed.
And once the operating system becomes part of the regulatory apparatus, the boundary between infrastructure and governance begins to dissolve.
9. Technical Challenges and Circumvention
If the legislative trajectory described so far suggests a coherent regulatory movement toward age verification, the technical reality is considerably less straightforward. Age verification systems are not merely difficult to design; they are inherently difficult to enforce in a global, decentralised network environment.
This difficulty is not incidental. It arises from a structural tension between the design of the internet and the objectives of regulators. The internet was built to route around obstacles. Age verification systems, by contrast, attempt to introduce friction and control points into a network that historically avoided them.
As a result, every age verification scheme encounters the same basic problem: once access restrictions exist, users will inevitably explore ways around them.
The mechanisms for doing so are neither exotic nor particularly difficult to obtain. In practice, several circumvention strategies are already widely understood.
Among the most common are the following:
- Virtual Private Networks (VPNs). These allow users to route traffic through different jurisdictions, bypassing region-specific restrictions.
- Adult accounts. Minors can create accounts using falsified birth dates or credentials belonging to adults.
- Device sharing. A child using a parent’s phone or computer inherits the identity attributes associated with that device.
- Browser access. Restrictions implemented through mobile applications can sometimes be bypassed by accessing services directly through a web browser.
- Jailbreaking or rooting devices. Modifying the operating system can disable enforcement mechanisms built into the device environment.
- Alternative platforms. When mainstream services impose restrictions, users often migrate to less regulated platforms.
None of these techniques require advanced technical expertise. Many are already common practice among technologically literate users.
This does not necessarily mean that age verification systems are ineffective. Regulators often acknowledge that perfect enforcement is unrealistic. Instead, the policy objective tends to be reducing exposure and raising the effort required to bypass restrictions rather than eliminating circumvention entirely.
Even so, the limitations of verification technologies remain significant.
9.1 Age Verification Methods and Their Weaknesses
Different technical approaches to age verification attempt to balance accuracy, privacy, and scalability. Each approach offers advantages, but none is without serious trade-offs.
| Method | Strength | Weakness |
|---|---|---|
| Self-reported age | Easy to implement | Trivial to bypass |
| ID verification | Highly accurate | Significant privacy risks |
| Facial age estimation | Scalable and automated | Accuracy limitations and bias |
| Cryptographic credentials | Privacy preserving | Technically complex and immature |
Self-reported age remains the simplest method and is still widely used across many platforms. However, its reliability is minimal; entering a false birth date requires little effort and no external verification.
Identity-document verification offers far greater accuracy but introduces substantial privacy concerns. Storing or transmitting government ID information creates obvious security risks, and many users are reluctant to share such credentials with commercial platforms.
Facial age estimation technologies attempt to strike a middle ground by using machine-learning models to estimate a user’s age from an image. These systems can operate quickly and without requiring official documents, but their accuracy varies and they often raise concerns about biometric data collection.
Cryptographic credential systems represent a more privacy-preserving approach. Instead of revealing a birth date or identity document, a trusted authority could issue a credential proving only that the user belongs to a certain age category. In theory, such systems allow verification without exposing personal information. In practice, they remain technically complex and difficult to deploy at global scale.
The result is an uncomfortable reality: every verification method solves one problem while introducing another.
9.2 The Open-Source Conflict Scenario
A further complication emerges when considering the role of open-source software ecosystems.
Much of the discussion surrounding age verification assumes that operating system vendors will implement the necessary APIs and enforcement mechanisms. For proprietary platforms such as iOS, Android, and Windows, this assumption may be reasonable. These systems are controlled by corporations that can modify their software in response to regulatory requirements.
Open-source operating systems operate under a different governance model.
Consider the case of Linux distributions. Unlike commercial operating systems, most Linux distributions are maintained by distributed communities of developers rather than a single corporate authority. If regulators mandate operating-system-level age verification APIs, the open-source community could theoretically decline to implement them.
This possibility raises a number of intriguing questions.
What happens if a large ecosystem of open-source systems simply refuses to comply with regulatory mandates?
Several responses might emerge.
| Actor | Reaction |
|---|---|
| Governments | Require compliance for devices sold within their jurisdiction |
| Platforms | Block access from operating systems lacking age-verification support |
| App stores | Restrict distribution of non-compliant software |
| Linux community | Fork distributions or operate outside regulated ecosystems |
Such a conflict would reveal a deeper tension between regulatory governance and open computing systems. Laws designed for centrally controlled platforms do not map easily onto decentralised software communities.
9.3 Regulation vs Open Systems
This dynamic can be visualised as a structural fork within the technology stack.
regulated platforms
↓
OS age API required
↓
proprietary OS | open source OS
compliance refusal
Proprietary operating systems, controlled by a small number of companies, can implement verification infrastructure relatively quickly. Open-source ecosystems, by contrast, are governed by consensus among distributed contributors who may not accept regulatory mandates imposed by external authorities.
In practice, this tension may lead to a fragmented landscape in which regulated platform ecosystems coexist with alternative computing environments that operate outside the regulatory framework.
Such fragmentation would not necessarily invalidate age-verification policies, but it would complicate enforcement and potentially drive some users toward less regulated technological spaces.
9.4 The Limits of Technical Control
These challenges highlight a broader lesson about the intersection of law and technology.
Regulation can mandate behaviour from platforms and infrastructure providers, but it cannot fully eliminate the adaptability of users within a distributed network. Every enforcement mechanism produces countermeasures; every restriction invites experimentation with ways around it.
The history of internet governance is filled with such cycles.
Age verification systems will almost certainly follow the same pattern. They will succeed in shaping platform behaviour and increasing friction for certain activities. At the same time, they will remain imperfect tools operating within a network that was never designed for strict identity enforcement.
The resulting system will likely be neither fully controlled nor fully open, but something in between, a negotiated balance between regulatory ambition and technological reality.
9.5 Platform Migration and Informal Communities
When access to mainstream platforms becomes restricted, users often migrate to alternative digital spaces rather than abandoning online interaction entirely.
Historically, this has included parts of the so-called dark web, but in practice many users move to more accessible environments such as private messaging platforms, encrypted groups, or large semi-private chat communities.
One of the most prominent examples is Discord, which hosts millions of user-created servers organised around shared interests or social groups. For many participants, these spaces function less as traditional social media platforms and more as informal community hubs, places to chat, share experiences, or simply avoid loneliness.
This pattern highlights an important limitation of regulatory approaches that focus on restricting access to specific platforms. Digital communities tend to reorganise rather than disappear. When certain environments become constrained, social interaction often shifts toward platforms or spaces that operate outside the immediate scope of regulation.
Understanding these migration dynamics is important when evaluating the likely real-world effects of age verification and youth social-media bans.
10. Economic Incentives Behind the System
Regulatory debates are often framed in moral or political terms, child safety, privacy, freedom of speech. Yet technological systems rarely evolve through ethical arguments alone. Beneath the visible layer of legislation and public concern lies another force that quietly shapes the direction of technological infrastructure: economic incentives.
Age verification is no exception.
While many of the laws discussed in earlier sections are motivated by genuine concerns about child welfare and digital harms, the mechanisms chosen to implement those policies interact in complex ways with the structure of the technology industry itself. In particular, they intersect with an existing concentration of power among a small number of platform and infrastructure providers.
Once age verification moves into the operating system layer, the economic dynamics of the system change.
10.1 Compliance Favours Scale
Large technology firms possess a structural advantage when new regulatory requirements emerge. Compliance with complex digital governance rules requires resources that smaller companies often lack: legal teams, compliance departments, security infrastructure, and engineering capacity.
For a global platform such as Apple, Google, or Microsoft, implementing an age-verification API may involve significant engineering work, but it remains a manageable extension of existing identity and security systems. These companies already operate:
- global account infrastructures
- secure credential storage systems
- large-scale identity management frameworks.
By contrast, smaller companies and independent developers may struggle to implement comparable systems. If regulators require integration with age-verification infrastructure, compliance becomes an additional technical and administrative burden.
The result is not necessarily deliberate regulatory capture. Rather, it is a familiar structural pattern: regulations designed to solve public problems often favour organisations already capable of operating at large scale.
10.2 Liability Moves Down the Stack
Another important economic effect concerns the distribution of legal responsibility.
When age verification is implemented at the level of individual platforms, each platform bears the burden of determining whether its users comply with regulatory requirements. This exposes the company directly to legal risk.
By moving verification deeper into the technology stack, into the operating system or device layer, much of that responsibility can shift toward infrastructure providers.
A simplified version of the logic looks like this:
- the operating system verifies the user’s age category
- applications receive the verified classification
- platforms enforce rules based on that classification.
In this model, platforms can argue that they rely on the identity attributes supplied by the operating system. If the classification proves inaccurate, responsibility may be distributed across multiple actors rather than falling solely on the application provider.
For large technology firms that control both operating systems and platforms, this shift can be particularly advantageous. It allows identity verification to become part of the infrastructure rather than a feature that each service must independently build and maintain.
10.3 Barriers to Entry
The most significant economic consequence may lie in how regulatory complexity affects competition.
Digital platforms historically benefited from relatively low barriers to entry. A small team of developers could build a new service and deploy it globally with limited regulatory overhead. While scaling such a service presented technical challenges, the initial act of launching a platform remained comparatively accessible.
Age-verification requirements introduce a new category of operational complexity. A platform that wishes to operate legally across multiple jurisdictions may now need to integrate with verification systems, enforce age-specific policies, and maintain compliance with evolving regulatory frameworks.
For large firms, these tasks are difficult but achievable. For smaller entrants, they may represent a prohibitive cost.
Over time, this dynamic can contribute to an industry structure in which regulatory compliance itself becomes a competitive advantage, one that favours organisations already large enough to absorb it.
10.4 Infrastructure as Governance
These economic dynamics reinforce the trend identified earlier in the article: the migration of internet governance from the application layer to the infrastructure layer.
Operating systems, identity providers, and app distribution platforms increasingly become the intermediaries through which regulatory rules are implemented. Companies controlling these layers gain influence not only over technical architecture but also over the economic environment in which digital services operate.
The resulting feedback loop can be summarised succinctly:
regulation → platform consolidation
Regulation increases the complexity of operating digital services. Complexity favours organisations capable of managing it. Those organisations consolidate their position as the primary gateways through which users access the internet.
10.5 An Unintended Consequence
None of this implies that policymakers intend to strengthen the dominance of existing technology giants. In many cases, the opposite is true; governments frequently express concern about the concentration of power within the technology sector.
Yet policy outcomes often diverge from policy intentions. When regulatory frameworks rely on infrastructure controlled by a small number of firms, those firms inevitably become central actors in the implementation of the rules.
Age verification illustrates this paradox clearly. Laws designed to protect children from harmful online environments may simultaneously reinforce the structural position of the companies that already control the most important layers of the digital ecosystem.
Understanding this interaction between regulation and market structure is therefore essential. Without it, discussions about age verification risk overlooking one of the most consequential aspects of the system being built: not only how it governs users, but how it reshapes the economic landscape of the internet itself.
11. Behavioural Collapse and Identity Signals
Up to this point the discussion has focused on regulatory frameworks, technical infrastructure, and institutional incentives. Yet these developments intersect with another dynamic that has been unfolding across digital systems for more than a decade: the gradual integration of human behaviour into machine optimisation processes.
In the Hard-Wired Wetware series I described this trajectory as a three-stage progression:
attention extraction
↓
behavioural collapse
↓
human integration into machine systems
The first phase, attention extraction, defined the early platform economy. Digital services competed to capture and retain user attention through increasingly sophisticated engagement mechanisms. Recommendation algorithms, infinite scrolling interfaces, and behavioural nudges emerged as tools for maximising the time users spent interacting with the system.
Over time, however, the scale and sophistication of these systems began to alter the environment in which human behaviour itself occurred. Users were no longer simply interacting with platforms; they were adapting to environments optimised by algorithms that continuously adjusted in response to their actions.
This dynamic produced what I described as behavioural collapse: the gradual compression of human behavioural diversity as users learn, consciously or unconsciously, to respond to the incentive structures embedded within algorithmic systems.
Under these conditions, platforms cease to function merely as communication channels. Instead, they become behavioural environments, systems designed to shape and predict patterns of human interaction.
Age verification introduces a new layer into this process.
11.1 Identity as Behavioural Metadata
From the perspective of platform optimisation systems, identity attributes function as highly valuable behavioural signals. They allow the system to categorise users before observing their behaviour, enabling algorithms to adjust the environment accordingly.
Age is particularly significant because it correlates strongly with patterns of media consumption, social interaction, and susceptibility to different forms of engagement design.
Once age verification becomes widely available at the infrastructure level, platforms can treat age as a first-class parameter within their optimisation models.
In practical terms, this means that the behavioural environment can be tuned differently for different user categories.
Platforms may optimise their systems differently for:
- children, whose interactions must comply with strict safety and developmental guidelines
- teenagers, whose engagement patterns and vulnerability to certain forms of content are considered distinct
- adults, who are generally granted broader access and fewer restrictions.
The algorithmic systems governing content visibility, interaction dynamics, and recommendation pathways can therefore be adjusted according to the user’s identity classification before the user even begins interacting with the platform.
This is not simply a regulatory compliance feature. It is also a data structure, a new variable that machine learning systems can incorporate into behavioural models.
11.2 The Feedback Loop
Once identity attributes become part of the behavioural environment, they enter the same feedback loop that already governs other aspects of digital interaction.
Platforms observe behaviour within each age category. The algorithms adjust the environment in response to that behaviour. Users then adapt their behaviour to the adjusted environment, producing new data that further refines the system.
The loop can be summarised as follows:
- identity attributes classify the user
- algorithms configure the information environment
- users respond to that environment
- behavioural data feeds back into optimisation systems.
The introduction of age verification therefore deepens the integration between human behaviour and machine optimisation.
What appears on the surface as a simple compliance mechanism, confirming whether a user is under eighteen, becomes, at the system level, an additional input into the continuous modelling of human behaviour.
11.3 Behavioural Segmentation
Digital platforms have always segmented users. Advertising systems already group individuals into demographic and behavioural categories, sometimes inferred through complex predictive models.
Age verification changes the nature of that segmentation. Instead of relying on probabilistic inference, the platform gains access to a verified identity attribute.
This reduces uncertainty within the system. Algorithms no longer need to estimate whether a user belongs to a particular demographic category; they can rely on an authoritative signal provided by the operating system or verification infrastructure.
In effect, identity attributes transform behavioural modelling from a process of inference into one of classification.
This may seem like a minor technical refinement. Yet in large-scale optimisation systems even small improvements in classification accuracy can produce significant shifts in how the system behaves.
11.4 From Users to Components
Within the broader framework of the Hard-Wired Wetware thesis, this development reflects the continuing evolution of digital platforms from communication systems into human-machine integration environments.
In such environments, users do not merely interact with technology. They become components within optimisation loops that continuously adapt to their behaviour.
Age verification contributes to this process by formalising one of the attributes through which users are categorised. Once incorporated into the system, that attribute becomes part of the machinery through which behavioural environments are constructed.
In other words, identity signals do not simply regulate access to digital spaces. They also participate in the ongoing process by which those spaces shape and stabilise patterns of human behaviour.
The regulatory motivations behind age verification may be rooted in child protection and platform safety. Yet the technical infrastructure being built has consequences that extend well beyond those original intentions.
It adds another layer to the system through which human activity becomes legible, classifiable, and ultimately optimisable by machines.
12. Asymmetric Integration and the Post-LLM Web
The dynamics described in the previous section, identity signals feeding into behavioural modelling, become even more consequential when considered alongside the structural transformation currently underway in artificial intelligence systems. The emergence of large-scale machine learning models, particularly large language models (LLMs), is not merely changing how information is produced. It is altering how human behaviour itself is integrated into computational systems.
In the Hard-Wired Wetware II article I described this emerging condition through the concept of Asymmetric Integration.
The core idea is relatively simple: modern digital systems no longer merely observe human behaviour. Increasingly, they integrate human behaviour into optimisation processes in which the machine system possesses far greater capacity to analyse, predict, and adapt than the humans participating in it.
This relationship is therefore fundamentally asymmetric.
Humans supply behavioural signals, attention, interaction patterns, and feedback loops, while machine systems process those signals at scale, continuously adjusting the informational environment in response. The system evolves faster than its participants can consciously perceive.
The dynamic can be visualised in its simplest form:
human behaviour
↓
platform data
↓
AI optimisation
↓
information environment
Human actions generate data. Platforms collect and structure that data. Machine-learning systems optimise the environment in response. The resulting information environment then shapes subsequent human behaviour, completing the feedback loop.
What distinguishes the current phase of this cycle is the increasing role of AI systems in managing the optimisation process itself.
12.1 Identity Signals and Algorithmic Systems: An Emerging Research Area
The interaction between identity attributes and algorithmic optimisation systems remains an emerging area of research. While many of the mechanisms described in this paper are technically plausible, the long-term behavioural consequences are not yet well understood.
Modern digital platforms rely heavily on machine-learning systems to determine how information is ranked, recommended, and presented to users. These systems already incorporate a wide range of behavioural signals derived from user interaction data.
Identity attributes, such as age classifications, may eventually become additional parameters within these optimisation systems. Verified demographic signals could allow platforms to tune recommendation models differently for different user groups or regulatory categories.
However, the extent to which identity signals will reshape algorithmic environments remains uncertain. The integration of identity infrastructure into platform systems may produce a range of outcomes, from improved safety mechanisms for younger users to more sophisticated forms of behavioural segmentation.
Understanding these dynamics will require further interdisciplinary research combining digital identity studies, platform governance analysis, and machine-learning research.
12.2 The Post-LLM Web
Large language models and related AI systems represent a new layer within digital platforms. They do not merely rank or filter content in the way earlier recommendation systems did. Instead, they are capable of generating, synthesising, and contextualising information dynamically.
This means the informational environment is no longer limited to selecting from existing content. The environment itself can now be constructed in real time by AI systems responding to behavioural signals.
In such an environment, the role of identity attributes becomes significantly more important.
Identity signals allow optimisation systems to segment the population into categories before interaction occurs. Instead of presenting a single informational environment to all users, platforms can create differentiated environments tailored to particular groups.
Age verification provides one of the first infrastructure-level signals enabling this process. Once the system can reliably distinguish between categories such as children, teenagers, and adults, the information environment can be tuned accordingly.
This tuning can take many forms:
- algorithmic filtering of content categories
- adjustment of recommendation models
- modification of interface design and interaction features
- variation in advertising and persuasion strategies.
What emerges is not merely a moderated information environment, but a segmented informational architecture.
12.3 Differentiated Persuasion Environments
One of the most significant consequences of this segmentation lies in how persuasive information flows through digital systems.
Persuasion is not a new phenomenon in media environments. Advertising, political messaging, and social influence have always operated through communication channels. What changes in algorithmically mediated systems is the precision with which persuasion can be targeted and the speed with which its effectiveness can be evaluated.
Identity attributes act as anchoring signals within this process. They allow machine-learning systems to begin the optimisation process with a set of prior assumptions about the user population.
This makes it possible to construct differentiated persuasion environments, information ecosystems tuned to the behavioural characteristics associated with particular groups.
For example:
- content visibility may be adjusted differently for minors than for adults
- recommendation systems may prioritise different types of narratives or media formats for teenage audiences
- interaction dynamics may be structured to encourage certain forms of engagement while discouraging others.
The system does not necessarily need to understand the underlying psychology of its users. It only needs to observe behavioural responses and adjust accordingly.
Over time, the informational environment becomes increasingly specialised for each user category.
12.4 Targeted Information Ecosystems
The result of this process is the gradual emergence of targeted information ecosystems.
Instead of a single shared digital environment, different categories of users encounter subtly different versions of the internet. The differences may not always be visible to individual participants, but they accumulate across recommendation pathways, search results, and algorithmic content feeds.
Age verification is not the only identity signal that could drive such differentiation, but it is among the first to be embedded at the infrastructure level. Once identity attributes become standard inputs to platform systems, additional attributes could theoretically be introduced in the future.
The implications extend well beyond regulatory compliance.
Age verification may initially exist to prevent minors from accessing harmful content. Yet once the signal is available to platform systems, it also becomes available to the optimisation loops governing information flow.
In other words, identity attributes become part of the machinery through which the post-LLM web organises human attention.
12.5 Integration Rather Than Interaction
Within the Asymmetric Integration framework, the most important insight is not that humans interact with machine systems, but that humans are increasingly integrated into them.
Human behaviour supplies the signals that guide optimisation. Machine learning systems analyse those signals and adapt the informational environment accordingly. The resulting environment shapes subsequent behaviour, completing the cycle.
Age verification contributes a new layer to this loop by providing an explicit identity parameter through which behaviour can be categorised before optimisation begins.
What begins as a regulatory mechanism therefore becomes part of the underlying architecture through which digital systems integrate human activity into computational processes.
The significance of this shift lies not in any single law or technical feature, but in the gradual transformation of the internet into a system where identity attributes, behavioural signals, and machine optimisation increasingly operate together.
And once those elements are integrated, the internet begins to function less like a network of information and more like a structured environment for managing human behaviour at scale.
13. The Internet Architecture Now Emerging: Part 1: Conceptual Explanation
Taken individually, the developments described in the previous sections might appear as separate trends: youth safety legislation, operating-system identity infrastructure, evolving platform governance frameworks, and increasingly powerful AI-driven recommendation systems. Yet viewed together they form something more consequential.
They form the outline of a new governance architecture for the internet itself.
This architecture does not emerge through a single regulatory initiative or technological breakthrough. Instead, it arises through the gradual interaction of several systems that were originally designed for different purposes. Governments introduce regulatory obligations; operating systems provide identity infrastructure; platforms enforce behavioural rules; algorithmic systems optimise information environments.
Once these layers begin to interlock, a new structure becomes visible.
13.1 Why Age Verification Appeared Everywhere at Once
Age verification did not emerge globally because governments suddenly coordinated around a new idea. For nearly two decades, policymakers attempted similar systems, most notably the UK’s 2017 pornography verification scheme, but they repeatedly failed due to technical limitations and lack of enforcement mechanisms.
What changed in the early 2020s was not the idea, but the infrastructure.
Three separate developments matured at roughly the same time: the consolidation of smartphone operating systems into a small number of platform providers, the emergence of digital identity systems capable of issuing attribute credentials, and the rise of platform governance laws requiring companies to mitigate online harms. Only when these systems converged did age verification become technically enforceable.
In this sense, the current wave of age verification laws is not simply a regulatory trend. It is the visible outcome of a deeper architectural convergence in the infrastructure of the modern internet.
13.2 Age Verification as the First Identity Attribute
Age verification may appear to be a narrow regulatory tool aimed at protecting children. In practice, however, it represents something much larger: the first widely deployed identity attribute within the architecture of the modern internet.
Historically, the web functioned as an anonymous or pseudonymous communication network. Individuals published information, and others evaluated it based on content, reputation, or social context. Age verification introduces a different model, in which access to information environments is mediated by persistent attributes associated with the user.
Once infrastructure exists to verify one attribute, age, it can easily support others. Systems capable of issuing age credentials can also issue credentials related to jurisdiction, identity verification, professional status, or institutional affiliation. In this sense, age verification should be understood not as a standalone policy intervention but as the first step in a broader transformation toward credential-mediated online environments.
The significance of this shift lies not in the specific attribute being verified, but in the architectural precedent it establishes. Age verification normalises the idea that access to digital spaces may depend on attributes associated with the user rather than the content they produce.
13.3 Toward a KYC-Style Attribute Governance Model for the Internet
The emerging model of internet regulation increasingly resembles the governance framework used in modern financial systems. In finance, institutions must identify their customers through “Know Your Customer” (KYC) procedures before allowing them to participate in transactions. Once verified, users are categorised into risk tiers that determine how they may interact with the system.
However, the comparison should be understood carefully. Traditional KYC systems verify full legal identity for financial compliance purposes, whereas most age-verification systems verify only a specific attribute, whether a user belongs to a particular age category. In this sense, the emerging model is better understood as a form of attribute governance rather than full identity governance.
Age verification introduces a similar logic to digital platforms. Instead of regulating individual pieces of content, regulators increasingly require platforms to classify users according to attributes such as age, jurisdiction, or identity status. Access to information environments is then mediated by these attributes. In this sense, the age-verification wave may represent the early stages of a broader transition toward a KYC-style governance model for the internet.
13.4 The Convergence of AI Governance, Platform Governance, and Age Verification
The regulatory landscape surrounding digital platforms often appears fragmented. Governments have introduced platform governance laws, age-verification mandates, and AI safety frameworks through separate legislative processes. Yet these initiatives increasingly form a coherent regulatory architecture.
All three categories of regulation address different layers of the same system: algorithmically mediated behavioural environments. Platform governance laws regulate the responsibilities of digital intermediaries. Age verification systems classify users so that platforms can apply differentiated rules. AI governance frameworks regulate the algorithms that shape information exposure. Together, these systems form a layered model of behavioural governance in which user attributes, platform policies, and algorithmic systems interact to structure digital environments.
Seen in this light, the age-verification wave is not an isolated development but part of a broader transformation in how governments regulate algorithmically mediated systems.
13.5 Uncoordinated Change Can Still Produce Structural Transformation
The architectural shift described in this article should not be interpreted as the result of a coordinated attempt by governments to redesign the internet. In most jurisdictions, age-verification policies have emerged in response to specific political pressures: concerns about youth mental health, online pornography, algorithmic harms, or platform accountability.
However, complex technological systems do not require central planning to undergo structural change. When multiple regulatory initiatives impose similar technical requirements across platforms, the resulting infrastructure adaptations can accumulate into broader architectural transformations.
In this sense, the emergence of identity-mediated internet systems may be better understood as a form of institutional convergence. Governments pursuing different policy goals often arrive at the same practical requirement: platforms must determine something about the user before allowing access. Age verification is simply the first attribute widely deployed within this evolving framework.
The resulting infrastructure may therefore reflect the interaction of regulatory incentives, technological constraints, and platform economics, rather than a deliberate project to redesign the internet.
13.6 Geopolitical Convergence: Why Every Major Power Wants the Same Stack
Although debates around age verification and digital identity are often framed as national policy issues, a broader geopolitical pattern is emerging. Across very different political systems, governments are converging on remarkably similar technical architectures for digital identity and online governance.
In China, real-name registration requirements have long linked online activity to verified identity credentials. In India, the Aadhaar system created one of the largest biometric identity infrastructures in the world, enabling both government services and private-sector verification. The European Union is developing the EU Digital Identity Wallet, intended to allow citizens to carry verifiable credentials issued by governments and trusted institutions. In the United States, while federal identity systems remain politically contentious, a growing patchwork of state-level age verification laws is creating pressure for comparable technical solutions.
These initiatives differ significantly in their political context, legal frameworks, and privacy protections. Yet they share a strikingly similar underlying architecture.
Across jurisdictions, digital identity systems increasingly rely on:
- portable identity credentials or wallets
- cryptographic verification of attributes
- platform-level enforcement mechanisms
- integration with operating systems and major technology platforms
In other words, governments with very different political traditions are converging on a common technical stack for identity verification and digital governance.
This convergence is not accidental. Digital environments increasingly operate at global scale, while regulatory authority remains national. Identity infrastructure offers governments a mechanism for asserting policy within globally distributed systems. By enabling platforms to classify users according to verified attributes, such as age, residency, or eligibility, regulatory objectives can be implemented within the architecture of digital services themselves.
The result is a form of infrastructural governance. Rather than relying solely on legal enforcement after the fact, policy objectives are embedded directly within the technical systems through which digital interactions occur.
Seen from this perspective, the rise of age verification is not simply a child safety policy initiative. It is one instance of a broader global shift toward identity-mediated governance of digital environments.
Different political systems may deploy this infrastructure in different ways. Yet the underlying technological trajectory appears increasingly shared.
14. The Internet Architecture Now Emerging II: System Architecture Walkthrough
At its simplest, the emerging architecture can be described as a vertical chain through which governance flows downward and behaviour flows upward.
regulation
↓
identity credentials
↓
OS identity layer
↓
platform governance
↓
algorithmic environments
↓
user behaviour
Each layer performs a distinct function, yet each depends on the layer above it and shapes the layer below.
14.1 Regulation as the Entry Point
The process begins with regulation. Governments define policy objectives, protecting minors from harmful content, limiting exposure to certain forms of media, or ensuring that platforms take responsibility for the environments they create.
These policies rarely specify technical implementation details. Instead, they establish obligations that platforms must satisfy. In the case of age-verification laws, the obligation is relatively straightforward: platforms must ensure that minors do not encounter restricted forms of content or interaction.
To fulfil that obligation, however, platforms must first determine whether a user is a minor.
14.2 Identity Credentials
This requirement introduces the next layer of the architecture: identity credentials.
Rather than verifying age independently for every service, the system increasingly relies on identity attributes that can be reused across multiple platforms. These attributes might include a user’s age category, parental consent status, or other credentials relevant to regulatory rules.
The credential itself does not necessarily reveal the user’s full identity. In many implementations, it simply states that the user belongs to a particular class, such as “under 16” or “over 18.” Yet even this limited information becomes a powerful organising principle for digital environments.
Identity attributes thus become the bridge between regulatory requirements and technological infrastructure.
14.3 The Operating System Identity Layer
Once identity credentials exist, they must be stored and managed somewhere within the technology stack. As discussed earlier, the operating system layer has emerged as the most practical location.
Operating systems already manage device identity, authentication systems, and secure credential storage. By incorporating age credentials into this layer, they become the intermediary through which identity attributes are exposed to applications.
This is the moment at which the architecture becomes infrastructural.
Instead of individual platforms verifying identity independently, the operating system becomes the certifying authority that provides identity signals to the software ecosystem running on the device.
14.4 Platform Governance
With identity attributes available through the operating system, platforms can implement the governance rules required by regulation.
A social network might restrict certain forms of content for minor users. A video platform might alter its recommendation model. Messaging systems might disable specific interaction features for younger audiences.
In this stage of the architecture, platforms translate identity signals into behavioural rules.
These rules may include:
- limiting access to specific categories of content
- modifying recommendation systems
- restricting communication features
- imposing time or usage limits.
The result is not merely moderation but the construction of differentiated platform environments for different classes of users.
14.5 Algorithmic Environments
At the next layer, algorithmic systems take those governance rules and incorporate them into the optimisation processes that determine what users actually see.
Modern platforms rarely present information in a neutral chronological stream. Instead, machine-learning models continuously select, rank, and generate content according to behavioural signals and platform objectives.
Once identity attributes become available, those attributes enter the optimisation process as additional parameters.
This means the informational environment itself can vary according to user classification. Two users interacting with the same platform may encounter subtly different information ecosystems depending on their identity attributes.
The system becomes capable of producing multiple parallel environments rather than a single shared one.
14.6 User Behaviour
Finally, at the bottom of the architecture sits the user.
Human behaviour generates the signals that sustain the entire system. Every click, pause, message, and search query feeds back into the data streams used to refine algorithmic models.
In earlier phases of the internet, these behavioural signals were relatively unstructured. Users arrived anonymously, and platforms inferred characteristics from their activity.
In the architecture now emerging, identity attributes structure the environment before behaviour even occurs. The user enters a system already configured according to their classification.
The behaviour that follows therefore reflects not only the user’s preferences but also the design of the environment itself.
14.7 A Layered Governance System
When viewed as a whole, the architecture resembles a layered governance system rather than a simple communication network.
Regulation defines the objectives. Identity credentials operationalise those objectives. Operating systems distribute the credentials. Platforms translate them into rules. Algorithms implement those rules within the information environment. Users then interact within the resulting system.
The process is iterative and self-reinforcing. Behavioural data flows upward through the system, informing further optimisation and sometimes further regulation.
What emerges is not a single centralised authority controlling the internet, but a distributed governance architecture embedded across multiple layers of technology and policy.
Age verification is one of the first major identity signals to be inserted into this architecture. It is unlikely to be the last.
The significance of the current moment therefore, lies not only in the specific policies being introduced but in the structural shift they reveal. The internet is gradually transforming from a loosely governed information network into a layered system in which identity, regulation, and algorithmic optimisation operate together.
And once that architecture is in place, it becomes the framework within which future digital governance will unfold.
15. Does This Actually Protect the People It Claims To?
Up to this point the analysis has focused largely on architecture: the regulatory frameworks emerging across jurisdictions, the identity infrastructure being inserted into operating systems, and the optimisation systems that shape the information environments users inhabit.
Yet architecture alone does not answer the most important question. The central justification for the regulatory wave now unfolding is not technical elegance or institutional coherence. It is protection.
Governments, regulators, and many advocacy groups argue that age verification systems are necessary to safeguard children from harmful online environments. These harms are typically described in terms of exposure to explicit content, predatory behaviour, bullying, and the addictive dynamics of algorithmically curated platforms.
If the emerging identity infrastructure is to be justified on those grounds, then the relevant question is simple: does it work?
The answer, at present, is complicated.
There is reason to believe that age verification systems may increase friction for certain activities. At the same time, there is remarkably little empirical evidence demonstrating that they substantially reduce the harms they are intended to address.
The effectiveness of the model depends on several assumptions that remain largely untested.
15.1 Does Age Verification Actually Protect Children?
The most immediate question is whether age verification mechanisms meaningfully prevent minors from accessing restricted services or content.
In principle, the logic appears straightforward. If platforms can determine whether a user is under a certain age, they can restrict access to certain environments or types of content.
In practice, however, the internet rarely behaves in ways that conform neatly to regulatory design.
Young users are often technologically adaptable and socially resourceful. Many of the techniques required to bypass age restrictions are widely understood and require little technical expertise.
Among the most common circumvention mechanisms are:
- the use of VPN services to access platforms from different jurisdictions
- creating accounts using false birth dates or borrowed adult credentials
- device sharing, where children access services through devices registered to parents or older siblings
- shifting activity from mainstream platforms to private or semi-private digital spaces.
These dynamics have already appeared in jurisdictions that have attempted to restrict youth access to specific platforms.
In many cases, younger users simply migrate toward environments where enforcement is weaker. These may include:
- smaller or less regulated social platforms
- private Discord servers
- encrypted messaging groups
- invitation-only communities.
Such environments can be far less visible to parents, educators, or regulators than the mainstream platforms they replace.
This raises an uncomfortable policy question: does friction equal protection?
Age verification may increase the effort required to access certain services, but increased friction does not necessarily eliminate the behaviour itself. Instead it may redirect it into spaces that are harder to monitor.
15.2 Does the System Reduce Online Harms?
Age-verification laws are often justified not only in terms of access restrictions but also in terms of reducing broader forms of online harm.
These harms typically include:
- cyberbullying
- online grooming
- exposure to harmful or self-destructive content
- addictive engagement patterns driven by algorithmic feeds.
Yet the relationship between age verification and these harms remains uncertain.
Even within the technology industry itself, there is growing recognition that many of these problems arise not simply from who uses platforms but from how the platforms themselves are designed.
Internal research from major social media companies has occasionally made this clear.
For example:
- Internal Snapchat analyses have acknowledged the addictive properties of certain engagement features.
- Documents disclosed during investigations into Meta (formerly Facebook) revealed that the company’s researchers understood how recommendation algorithms could amplify engagement loops among young users.
These findings suggest that the architecture of platform optimisation, particularly the emphasis on engagement and retention, plays a central role in shaping user behaviour.
Age verification does not fundamentally alter that architecture.
Even if platforms successfully distinguish between adults and minors, their core business incentives remain the same. Most large social media companies continue to optimise their systems around metrics such as:
- engagement
- attention
- session length
- user retention.
These optimisation targets can produce highly stimulating environments regardless of the user’s age category.
In other words, age verification may change who enters the system, but it does not necessarily change how the system itself operates.
15.3 The Role of Anonymity
Another dimension of the debate concerns anonymity.
Critics of age verification often frame the issue primarily as a question of privacy or surveillance. While those concerns are real, anonymity also serves important social functions within digital environments.
For many users, the ability to participate without attaching a fully verified identity provides a form of protection.
Groups that rely heavily on anonymous or pseudonymous participation include:
- domestic abuse survivors attempting to communicate without being located by violent partners
- whistleblowers exposing wrongdoing within organisations
- political dissidents operating in restrictive regimes
- journalists communicating with confidential sources
- LGBTQ youth seeking support in environments where their identity may be socially or legally dangerous.
In such cases, anonymity functions less as a tool for evading responsibility and more as a mechanism for personal safety.
Identity-linked access systems do not necessarily eliminate anonymity altogether. In many proposed models, the platform may only see an age classification rather than the user’s real identity.
However, the underlying infrastructure often requires identity information to exist somewhere within the system, held by an identity provider, a verification service, or an operating-system credential store.
The result is a form of conditional anonymity.
Users may appear anonymous within a particular platform, but their identity attributes exist elsewhere within the technical architecture. This arrangement can preserve some aspects of pseudonymity while still enabling regulatory enforcement, but it also introduces new points of vulnerability.
The implications for vulnerable communities remain uncertain.
15.4 Does the New Internet Become Kinder?
Beyond these technical and social questions lies a more philosophical one.
Even if age verification succeeds in protecting some children from certain forms of content, what kind of internet does it ultimately produce?
One possible future is relatively optimistic.
In this scenario, identity infrastructure enables platforms to create safer environments for younger users. Content harmful to minors becomes harder to access, recommendation systems are tuned more carefully, and parents gain more effective tools for managing digital exposure.
The resulting ecosystem might include:
- stronger moderation systems
- improved parental control mechanisms
- reduced exposure to explicit or harmful content.
Yet another scenario is equally plausible.
In this alternative trajectory, the underlying optimisation logic of digital platforms remains unchanged. Algorithms continue to maximise engagement and attention, and identity signals simply allow those systems to target users more precisely.
Rather than weakening behavioural optimisation, identity verification could even strengthen it. Verified demographic attributes allow platforms to refine their behavioural models with greater accuracy.
Within the framework described earlier in this article, this would deepen the dynamics of asymmetric integration.
Platforms would gain more reliable information about the users interacting with their systems. That information would feed into behavioural modelling processes designed to maximise engagement and retention.
In such an environment, the internet might become more structured, more regulated, and perhaps more segmented, without necessarily becoming less addictive or less behaviourally manipulative.
15.5 Protection or Reconfiguration?
The purpose of this section is not to dismiss the motivations behind age-verification policies. Protecting children from harmful digital environments is a legitimate and important objective.
However, evaluating the effectiveness of the current regulatory model requires distinguishing between intentions and outcomes.
Age verification may indeed reduce certain forms of exposure and create additional barriers for harmful interactions. At the same time, it does not address many of the structural incentives that shape platform behaviour.
The deeper transformation described throughout this article, therefore, remains relevant.
The internet is not simply becoming safer or more restricted. It is being reconfigured, technically, economically, and behaviourally, around a new architecture in which identity attributes, algorithmic optimisation, and regulatory governance interact in ways that are still only beginning to become visible.
15.6 The Policable Majority
In practice, most regulatory systems do not eliminate rule violations entirely. Instead, they influence the behaviour of the majority of participants while a smaller number of determined actors continue to find ways around restrictions.
Law-enforcement practitioners sometimes describe this dynamic informally through the observation that “police tend to police the policable.” Regulatory systems are typically most effective at shaping the behaviour of individuals who are already inclined to follow rules or who face moderate barriers to non-compliance.
Digital governance systems often operate in a similar manner. Age verification may not prevent all minors from accessing restricted services, just as speed limits do not prevent all drivers from exceeding them. However, such mechanisms can still alter behaviour across a large portion of the user population by introducing friction, inconvenience, or institutional consequences.
For this reason, evaluating the impact of age-verification systems solely through the lens of perfect enforcement may be misleading. Even imperfect classification mechanisms can reshape platform incentives, influence user behaviour, and justify the deployment of broader identity infrastructure within digital environments.
The significance of these systems therefore lies not only in whether they prevent every instance of circumvention, but in how they restructure the governance architecture through which online participation is organised.
16. Implications for the Future of the Internet
If the trajectory described in this paper continues, the emergence of identity-mediated infrastructure is likely to have several significant implications for the future architecture of the internet.
16.1 Anonymity and Pseudonymity
The early internet allowed users to access most online services without revealing their real-world identity. While pseudonymous interaction will likely continue in many contexts, the expansion of identity verification systems may gradually reduce the range of environments where complete anonymity is possible.
Rather than eliminating anonymity outright, identity infrastructure may create a more stratified internet in which different environments require different levels of credential verification. Some spaces may remain open and anonymous, while others increasingly require verified attributes.
16.2 Platform Governance Power
As identity attributes become integrated into operating systems, platforms, and digital infrastructure, technology companies may gain new forms of governance power.
Platforms that control operating systems, app stores, identity wallets, or verification frameworks could become key intermediaries in enforcing regulatory requirements. This may further concentrate influence in a relatively small number of infrastructure providers capable of implementing identity-based controls at scale.
A central question, therefore, emerges: whether identity infrastructure embedded within digital systems genuinely serves the public interest or instead consolidates governance authority within a small number of infrastructure providers. Digital Public Infrastructure (DPI) frameworks emphasise inclusivity, accountability, and open access. Yet when identity verification becomes embedded within operating systems and platform ecosystems, the governance of digital participation may increasingly be shaped by corporate infrastructure providers rather than public institutions.
Digital Public Infrastructure is frequently presented as a beneficial foundation for digital services and economic participation. However, there may also be darker architectural consequences when identity infrastructure becomes deeply embedded in digital environments. DPI frameworks typically emphasise public value and service delivery. Yet when identity infrastructure intersects with algorithmic platforms, recommendation systems, and behavioural optimisation architectures, identity attributes may begin to shape the environments users experience before interaction occurs. In this scenario, identity infrastructure extends beyond administrative verification and becomes part of the governance architecture of digital spaces themselves.
16.3 AI Systems and Identity Attributes
The emergence of AI-driven systems adds another dimension to identity-mediated environments.
Algorithmic systems increasingly determine what users see, which services they can access, and how online environments are structured. Identity attributes, such as age classifications or other verified credentials, may become inputs into these optimisation systems.
This could allow digital environments to be tailored not only according to behavioural signals but also according to verified characteristics of the user.
16.4 Identity Credentials Beyond Age
Age verification is likely to be only the first widely deployed identity attribute within internet infrastructure.
Once systems exist to verify and transmit cryptographically signed credentials, the same mechanisms could support other forms of attribute verification. These might include residency, eligibility for services, professional qualifications, or other regulatory categories.
The technical infrastructure built to address one policy objective may therefore create the foundation for a much broader identity layer within the internet.
16.5 A Structural Shift
Taken together, these developments suggest a gradual shift in how digital environments are governed.
The early internet was largely open by default, with moderation applied after interaction occurred. Identity-mediated systems operate differently: they allow digital environments to be structured according to verified characteristics before interaction takes place.
This represents a subtle but significant change in the architecture of online systems. Whether it ultimately produces more accountable digital spaces, more controlled environments, or some combination of both will depend not only on the technology itself, but on the governance frameworks that shape how it is used.
16.6 Societal Synchronisation and Algorithmic Environments
The architectural shift described in this article may also have implications beyond digital governance. It touches on the mechanisms through which human societies coordinate behaviour across populations.
Complex social systems depend on synchronisation mechanisms that align behaviour across large groups of people. Historically, these mechanisms emerged through cultural institutions, shared environments, and generational structures that helped stabilise social dynamics over time.
Several recent essays have explored how disruptions to these mechanisms can produce destabilising effects in complex societies. Research into phenomena such as behavioural sinks, demographic birth gaps, and algorithmic environments suggests that social instability can emerge when artificial control systems begin to replace organic coordination mechanisms.
Behavioural sinks do not emerge solely from abundance or technological change. They often arise when the mechanisms that synchronise behaviour across populations become distorted or fragmented.
Digital platforms increasingly function as coordination systems within modern societies. Algorithmic environments influence how individuals encounter information, form communities, and align their behaviour with others.
As identity attributes become embedded within these environments, the architecture of digital systems may begin to influence not only how information flows, but also how social synchronisation itself occurs.
The long-term implications of this shift remain uncertain. Yet it suggests that identity-mediated infrastructure may ultimately play a role in shaping the behavioural dynamics of large-scale digital societies.
16.6.1 Adjacent Work on Societal Changes
In previous essays, I explored this dynamic in more detail, focusing on birth gaps, reproductive desynchronisation, and algorithmic environments as potential modern analogues.
- Conflicting Social Dynamics: Population Collapse Versus Behavioural Sink explores how behavioural sinks emerge when social coordination mechanisms break down.
- Reproductive Desynchronisation, Birth Gaps and Behavioural Sink examines how demographic birth gaps can destabilise generational synchronisation in modern societies.
- Ontological Desynchronisation: From Birth Gaps and Behavioural Sinks to Algorithmic Capture extends the argument into digital environments where algorithmic systems begin to mediate social coordination itself.
16.7 Human Integration in the Post-LLM Web
A second implication concerns the changing nature of human–computer interaction.
For much of the history of the web, digital platforms competed primarily for human attention. Advertising-driven systems were designed to capture and retain user engagement within algorithmically curated information environments.
Recent developments in artificial intelligence suggest that a new phase may be emerging.
Large language models and generative systems can now produce vast volumes of content, conversation, and simulated social interaction. Digital environments are increasingly capable of generating narratives, communities, and informational ecosystems at scale.
In this context, the role of human participants begins to change.
Machines can increasingly generate the environment itself. What they still require from human users is something different: legitimacy.
Human presence provides validation, social grounding, and behavioural input that machine-generated systems alone cannot fully replicate. This creates a new form of interaction in which human users become integrated participants within environments increasingly shaped by algorithmic systems.
In earlier essays, this transition has been described as a movement from attention extraction toward human integration within machine-mediated environments. One possible model of this transition is the Asymmetric Integration Model (AIM), which describes how human and machine contributions may become unevenly distributed within digital ecosystems.
If identity attributes become integrated into the infrastructure of these environments, they may influence not only how users access digital spaces, but also how humans themselves become incorporated into algorithmically generated systems.
The result could be an internet in which identity, governance, artificial intelligence, and human participation are increasingly intertwined.
16.7.1 Prior Work on Sociological Changes in HCI
Hard-Wired Wetware is a four-part series examining the structural evolution of the post-LLM web and introducing the Asymmetric Integration Model (AIM).
- Hard-Wired Wetware I: From Attention Extraction to Human Integration outlines the transition from attention extraction to human integration.
- Hard-Wired Wetware II: The Post-LLM Web Asymmetric Integration Model (AIM) Defined defines the Asymmetric Integration Model (AIM).
- Hard-Wired Wetware III: Rebalancing the Asymmetric Integration Model (AIM) explores potential design interventions to rebalance the system.
- Hard-Wired Wetware IV: The Case Against Rebalancing — Why the Asymmetric Integration Model (AIM) May Be Self-Correcting examines the counter-argument that the asymmetry may be self-correcting.
Taken together, the series moves from diagnosis to model, from intervention to counter-argument, presenting AIM as both an explanatory framework and a testable structural hypothesis about the evolving architecture of the web.
17. Conclusion: What Architecture Is Emerging?
Debates about internet governance have a tendency to become trapped in the language of individual controversies. A new law appears and the discussion quickly polarises around familiar questions: Is this censorship? Is it necessary regulation? Does it threaten free speech? Does it protect vulnerable users?
These questions matter, but they are not the most important ones.
17.1 Beyond the Immediate Policy Debate
The transformation described throughout this article is not primarily about a single law or a particular regulatory controversy. It is about the gradual emergence of a new architectural layer within the internet itself.
The developments described throughout this article correspond to the transition toward the identity-mediated internet architecture shown in Figure 1, “Evolution of Internet Architecture (1990–2035)”.
Across multiple jurisdictions and technological systems, the same structural pattern is beginning to appear. Governments introduce obligations intended to protect certain groups of users. To enforce those obligations, platforms require reliable information about who those users are. To provide that information at scale, identity attributes become embedded within operating systems and digital identity infrastructure. Platforms then use those attributes to shape the information environments presented to users.
The result is not merely a new regulatory framework. It is the construction of a new type of digital system.
17.2 From Open Network to Identity-Mediated Infrastructure
Historically, the internet operated as a largely open network in which identity was optional, and governance occurred primarily after information appeared. Users could participate pseudonymously, and moderation mechanisms responded to content after the fact.
The architecture now emerging reverses that relationship.
Instead of beginning with open access, the system increasingly begins with classification. Identity attributes, initially age, but potentially others in the future, determine how digital environments are configured before interaction takes place.
The shift can be summarised in simple terms.
The internet is undergoing a structural transition from an open, largely anonymous network toward an identity-mediated information infrastructure.
Age verification represents the first large-scale deployment of this model. From a policy perspective, this transformation reflects a broader global movement toward Digital Public Infrastructure. Governments increasingly view identity systems as foundational infrastructure enabling access to digital services. Age verification requirements may therefore represent one of the first large-scale deployments of identity attributes within the operational architecture of the internet itself. In this sense, child-safety legislation may be acting as the catalyst through which identity infrastructure becomes embedded within the technical foundations of the web.
It introduces a globally recognisable identity attribute, whether a user is a minor or an adult, into the technological layers through which digital services operate. Once that attribute exists within the infrastructure, it becomes available to platforms, algorithms, and governance systems that rely on it to structure user experiences.
Seen in isolation, age verification may appear to be a narrow regulatory tool designed to address specific harms affecting children online. Seen in architectural context, it is something more consequential: the first widely deployed identity signal within a system increasingly organised around identity.
17.3 Power Within the Identity Layer
This raises a set of questions that extend far beyond the immediate policy debate.
If identity attributes become embedded within the infrastructure of digital systems, several issues become central:
- Who controls the identity layers through which users are classified?
- How are those systems governed, and by whom?
- What forms of authority do infrastructure providers acquire when identity becomes part of the technology stack?
These questions are not merely technical. They concern the distribution of power within the digital environment.
Operating system providers, identity verification services, and major platforms increasingly occupy positions within the architecture that resemble governance roles. They manage the systems that determine how identity attributes are generated, stored, and transmitted. In doing so, they influence how regulatory obligations are implemented and how informational environments are structured.
17.4 Identity Attributes Inside Algorithmic Systems
At the same time, algorithmic systems continue to evolve. Recommendation engines, generative AI models, and behavioural optimisation systems increasingly shape how users encounter information online. Once identity attributes are integrated into these systems, they become parameters within the optimisation loops that govern digital interaction.
The consequences of that integration remain uncertain.
One possibility is that identity infrastructure allows platforms to build safer environments, particularly for younger users. Content harmful to minors may become harder to access, and regulatory frameworks may gain greater leverage over the behaviour of digital services.
Another possibility is more ambiguous. Identity signals could simply become additional inputs to behavioural optimisation systems that already shape how human attention is captured and directed. In that case, the architecture being built would not merely regulate the internet, it would deepen the integration of human behaviour into machine-driven information systems.
The distinction matters.
Public debate often frames the issue in terms of censorship versus freedom. Yet the deeper transformation is not simply about which content is allowed or prohibited. It is about the structure of the environment through which information flows and behaviour is organised.
17.5 The Beginning of a Structural Shift
Large technological systems are often transformed not through single decisions but through the accumulation of many small regulatory and technical adjustments that gradually reshape the underlying architecture.
Age verification is only the beginning of that transformation.
As identity attributes become embedded in digital infrastructure, the internet itself begins to change character. It becomes less like a network of open communication and more like a layered system in which identity, governance, and algorithmic optimisation operate together.
Whether that system ultimately protects users or integrates them more deeply into behavioural optimisation environments will depend on how these identity layers evolve, and on who ultimately controls them.
Age verification may therefore represent more than a regulatory mechanism for protecting children online. It may also represent the first widely deployed identity attribute embedded within the infrastructure of the Internet itself. Once identity attributes become normalised within browsers, operating systems, and digital services, additional attributes, such as citizenship, credentials, or eligibility, may follow. The resulting architecture could gradually transform the internet from an open network defined by anonymous participation into an environment where access to digital spaces is increasingly mediated by verifiable identity characteristics.
The question is no longer simply how the internet should be regulated. It is how the identity layers now being embedded within its architecture will shape the environments through which human societies increasingly organise themselves.
18. Appendices
- 18.1 Appendix A: Global Map of Age Verification Laws
- 18.2 Appendix B: Technical Implementation Models
- 18.3 Appendix C: An Infrastructure Still in Formation
- 18.4 Appendix D: Bibliography
- 18.5 Appendix E: Media, Government Reports, and Institutional Sources
- 18.6 Appendix F: Optional Suggested Reading
- 18.7 Appendix G: Media Timeline of Age-Verification and Online Safety Regulation (2015–2026)
18.1 Appendix A: Global Map of Age Verification Laws
The regulatory developments described throughout this article are not confined to a single jurisdiction or political bloc. Age verification has emerged as a policy instrument across a wide range of legal and technological environments. While the specific mechanisms differ, from social media bans to identity verification requirements, the underlying objective remains consistent: determining whether a user belongs to a particular age category before granting access to certain forms of digital interaction.
What is striking is the geographical breadth of the trend. Countries with very different political systems, legal traditions, and technology ecosystems have begun moving in similar directions.
In some regions, age verification already forms part of active regulatory frameworks. These include:
- United Kingdom, through the Online Safety Act and associated regulatory requirements for “highly effective age assurance.”
- Australia, which has introduced one of the most stringent youth social media restrictions, prohibiting platform access for users under sixteen.
- Germany, where youth media protection laws already require strong safeguards against minors accessing harmful online content.
- South Korea, which has historically experimented with identity-linked online participation through its real-name registration policies.
- China, where extensive digital identity infrastructure already governs participation in many online services.
- United Arab Emirates, where digital identity systems are integrated into a wide range of online government and commercial services.
- Saudi Arabia, which has implemented identity-linked digital services across multiple sectors.
In several other jurisdictions, age verification laws are either under active development or being debated within national legislatures. These include:
- France, which has introduced social media access restrictions requiring parental consent for younger users.
- Spain, where policymakers are considering stronger youth protection rules for digital platforms.
- Norway, which has proposed raising the minimum age for social media participation.
- Denmark, where regulators are exploring additional restrictions on youth access to online platforms.
- Brazil, where legislative discussions around digital platform governance increasingly include identity verification mechanisms.
- Mexico, which has considered policies linking telecommunications services and digital identity frameworks.
- United States, where numerous state-level initiatives have introduced various forms of age verification requirements.
The result is not a uniform global policy regime but a diffusion of similar regulatory ideas across different governance contexts. Some systems emphasise parental consent, others rely on identity verification technologies, and still others incorporate age assurance into broader digital identity frameworks.
Yet the convergence remains notable. Across continents, policymakers are gradually arriving at the same operational premise: platforms cannot regulate youth access without first determining the age status of their users.
18.2 Appendix B: Technical Implementation Models
If the policy objective is age verification, the practical question becomes how that verification can actually be implemented.
Several technical models currently exist, each attempting to balance three competing priorities:
- accuracy — ensuring that users are classified correctly
- privacy — minimising the collection and exposure of personal data
- scalability — enabling the system to operate across billions of users.
No single method satisfies all three criteria simultaneously, and each approach carries its own trade-offs.
18.2.1 Self-Reported Age
The simplest and most widely used approach is self-reported age. Platforms simply ask users to provide a birth date during account creation.
This model has several advantages. It is easy to implement, imposes minimal friction on users, and does not require additional infrastructure.
However, it is also the least reliable method. Users, particularly younger ones, can easily enter false birth dates in order to bypass restrictions.
As a result, self-reported age systems tend to function more as policy signalling mechanisms than as effective verification tools.
18.2.2 Identity Document Verification
A more robust approach involves verifying age through government-issued identity documents, such as passports or national identity cards.
Under this model, users upload or present official identification to a verification service that confirms whether they meet the required age threshold.
This method offers high accuracy but raises significant concerns about privacy and data security. Storing or transmitting identity documents creates obvious risks, particularly when handled by commercial platforms or third-party verification providers.
For many users, the idea of providing government identification in order to access online services represents a substantial barrier to participation.
18.2.3 Facial Age Estimation
Another increasingly common technique relies on machine learning models capable of estimating a user’s age from facial images.
In such systems, users briefly present their face to a camera, and the software estimates whether they appear to fall above or below a certain age threshold.
This method offers scalability and avoids the need for official identity documents. However, its accuracy remains variable. Age estimation models may perform unevenly across different demographics and can generate both false positives and false negatives.
Furthermore, the collection of biometric data introduces its own privacy concerns.
18.2.4 Cryptographic Credentials
A more sophisticated approach involves cryptographic age credentials.
In this model, a trusted authority verifies the user’s age once and then issues a digital credential confirming that the user belongs to a specific age category. The credential can later be presented to platforms without revealing the user’s underlying identity information.
For example, a system might allow a user to prove that they are “over 18” without disclosing their exact birth date.
This approach offers strong privacy protections in theory, but implementing such systems at global scale requires complex identity infrastructure and cooperation between multiple institutions.
At present, most deployments remain experimental.
18.3 Appendix C: An Infrastructure Still in Formation
Taken together, these technical models illustrate a broader point: the infrastructure required to support global age verification is still evolving.
No single method has yet emerged as the universal solution. Instead, platforms and regulators are experimenting with a range of approaches, each balancing competing priorities in different ways.
What unites them is not the specific technology but the underlying architectural shift they represent.
For the first time in the history of the internet, large-scale systems are being developed to determine the identity attributes of users before granting access to digital environments.
Age verification is the first attribute being implemented at global scale. It will likely not be the last.
18.4 Appendix D: Bibliography
- 18.1 Appendix A: Global Map of Age Verification Laws
- 18.2 Appendix B: Technical Implementation Models
- 18.3 Appendix C: An Infrastructure Still in Formation
- 18.4 Appendix D: Bibliography
- 18.5 Appendix E: Media, Government Reports, and Institutional Sources
- 18.6 Appendix F: Optional Suggested Reading
- 18.7 Appendix G: Media Timeline of Age-Verification and Online Safety Regulation (2015–2026)
18.4.1 Legislation and Regulatory Frameworks
- Australian Parliament (2024) Online Safety Amendment (Social Media Minimum Age) Act 2024. Canberra: Parliament of Australia.
Available at: https://www.aph.gov.au/Parliamentary_Business/Bills_LEGislation - Department for Science, Innovation and Technology (2025) Online Safety Act: Explainer. London: UK Government.
Available at: https://www.gov.uk/government/publications/online-safety-act-explainer - European Commission (2023) The Digital Services Act: Ensuring a safe and accountable online environment. Brussels: European Commission.
Available at: https://digital-strategy.ec.europa.eu/en/policies/digital-services-act - European Commission (2025) Guidelines on the Protection of Minors under the Digital Services Act. Brussels: European Commission.
Available at: https://digital-strategy.ec.europa.eu/en/library/protection-minors-digital-services-act-guidelines - European Parliament and Council (2022) Regulation (EU) 2022/2065 on a Single Market for Digital Services (Digital Services Act).
Available at: https://eur-lex.europa.eu/eli/reg/2022/2065/oj - UK Parliament (2023) Online Safety Act 2023. London: Legislation.gov.uk.
Available at: https://www.legislation.gov.uk/ukpga/2023/50 - California State Legislature (2023) California Age-Appropriate Design Code Act. Sacramento: California Legislative Information.
Available at: https://leginfo.legislature.ca.gov/faces/billTextClient.xhtml?bill_id=202120220AB2273 - Florida Legislature (2024) HB 3: Online Protections for Minors. Tallahassee: Florida Legislature.
Available at: https://www.flsenate.gov/Session/Bill/2024/3 - Utah Legislature (2023) Social Media Regulation Act. Salt Lake City: Utah State Legislature.
Available at: https://le.utah.gov/~2023/bills/static/SB0152.html - Texas Legislature (2023) HB 1181: Age Verification for Online Pornographic Content. Austin: Texas Legislature.
Available at: https://capitol.texas.gov/tlodocs/88R/billtext/html/HB01181F.htm - Louisiana Legislature (2022) Act 440: Age Verification for Pornographic Content. Baton Rouge: Louisiana Legislature.
Available at: https://legis.la.gov/legis/BillInfo.aspx?s=22RS&b=HB142
18.4.2 Digital Platform Governance and Regulation
- Ashurst LLP (2023) The UK Online Safety Act: Implications for Digital Platforms. London: Ashurst.
Available at: https://www.ashurst.com/en/insights/uk-online-safety-act-2023 - DigitalEurope (2025) Protection of Minors under the Digital Services Act. Brussels: DigitalEurope.
Available at: https://www.digitaleurope.org/policy-areas/digital-services-act - Codreanu, M. and Zamă, I. (2025) EU’s Digital Shield: New Rules to Protect Minors Online. Chambers & Partners.
Available at: https://chambers.com/articles/eu-s-digital-shield-new-rules-to-keep-minors-safe-online - Solarova, S., Mesarčík, M., Pecher, B. and Srba, I. (2026) ‘Beyond the Checkbox: Strengthening DSA Compliance through Social Media Algorithmic Auditing’, arXiv.
Available at: https://arxiv.org/abs/2602.12345 - Trujillo, A., Fagni, T. and Cresci, S. (2023) ‘The DSA Transparency Database: Auditing Moderation Actions by Social Media Platforms’, arXiv.
Available at: https://arxiv.org/abs/2309.05020 - Gorwa, R. (2019) ‘What is platform governance?’, Information, Communication & Society, 22(6), pp. 854–871.
Available at: https://doi.org/10.1080/1369118X.2019.1573914 - Klonick, K. (2018) ‘The New Governors: The People, Rules, and Processes Governing Online Speech’, Harvard Law Review, 131(6), pp. 1598–1670.
Available at: https://harvardlawreview.org/2018/04/the-new-governors
18.4.3 Identity Infrastructure and Digital Identity Theory
- Cameron, K. (2005) The Laws of Identity. Microsoft Corporation.
Available at: https://www.identityblog.com/stories/2005/05/13/TheLawsOfIdentity.pdf - Berners-Lee, T. (2018) Solid: A Decentralized Web Platform for Personal Data. MIT.
Available at: https://solidproject.org - World Wide Web Consortium (W3C) (2022) Decentralized Identifiers (DID) v1.0. W3C Recommendation.
Available at: https://www.w3.org/TR/did-core - World Wide Web Consortium (W3C) (2022) Verifiable Credentials Data Model 1.1. W3C Recommendation.
Available at: https://www.w3.org/TR/vc-data-model - National Institute of Standards and Technology (NIST) (2017) Digital Identity Guidelines (SP 800-63-3). Gaithersburg, MD: NIST.
Available at: https://pages.nist.gov/800-63-3 - Allen, C. (2016) ‘The Path to Self-Sovereign Identity’.
Available at: https://www.lifewithalacrity.com/2016/04/the-path-to-self-sovereign-identity.html - Windley, P. and Reed, D. (2022) Self-Sovereign Identity: Decentralized Digital Identity and Verifiable Credentials. Manning.
Available at: https://www.manning.com/books/self-sovereign-identity
18.4.4 Surveillance Capitalism and Algorithmic Governance
- Zuboff, S. (2019) The Age of Surveillance Capitalism. London: Profile Books.
Available at: https://www.hup.harvard.edu/books/9781610395694 - Cuéllar, M.F. (2020) ‘Economies of Surveillance’, Harvard Law Review, 133(4), pp. 1280–1336.
Available at: https://harvardlawreview.org/2020/02/economies-of-surveillance - Curran, D. (2023) ‘Surveillance Capitalism and Systemic Digital Risk’, Big Data & Society, 10(1).
Available at: https://journals.sagepub.com/doi/10.1177/20539517231177621 - Center for Humane Technology (2021) The Attention Economy and Social Media Design.
Available at: https://www.humanetech.com - Pasquale, F. (2015) The Black Box Society: The Secret Algorithms That Control Money and Information. Harvard University Press.
Available at: https://www.hup.harvard.edu/books/9780674368279
18.4.5 Youth Online Safety and Social Media Research
- US Department of Health and Human Services (2023) Surgeon General’s Advisory on Social Media and Youth Mental Health.
Available at: https://www.hhs.gov/surgeongeneral/priorities/social-media/index.html - American Psychological Association (2023) Health Advisory on Social Media Use in Adolescence.
Available at: https://www.apa.org/topics/social-media-internet/health-advisory-adolescent-social-media-use - Haidt, J. (2024) The Anxious Generation. Penguin.
Available at: https://www.anxiousgeneration.com - Haidt, J. and Rausch, Z. (2026) ‘Social Media Is Harming Young People at a Global Scale’.
Available at: https://www.anxiousgeneration.com/research - Pew Research Center (2025) Teens, Social Media and Mental Health. Washington, DC.
Available at: https://www.pewresearch.org/internet - Khalaf, A.M. et al. (2023) ‘Impact of Social Media on Adolescent Mental Health: A Systematic Review’, Cureus, 15(8).
Available at: https://www.ncbi.nlm.nih.gov/pmc/articles/PMC10476631 - van der Wal, A. et al. (2025) ‘Diverse Platforms, Diverse Effects: Evidence from a 100-Day Study on Social Media and Adolescent Mental Health’, Current Psychology.
Available at: https://link.springer.com/article/10.1007/s12144-025-08893-7
18.4.6 Internet Governance and Platform Power
- Lessig, L. (1999) Code and Other Laws of Cyberspace. New York: Basic Books.
Available at: https://codev2.cc - Benkler, Y. (2006) The Wealth of Networks. Yale University Press.
Available at: https://www.benkler.org/Benkler_Wealth_Of_Networks.pdf - Zittrain, J. (2008) The Future of the Internet – And How to Stop It. Yale University Press.
Available at: https://futureoftheinternet.org - Gillespie, T. (2018) Custodians of the Internet. Yale University Press.
Available at: https://yalebooks.yale.edu/book/9780300235029/custodians-of-the-internet - Khan, L. (2017) ‘Amazon’s Antitrust Paradox’, Yale Law Journal, 126(3).
Available at: https://www.yalelawjournal.org/note/amazons-antitrust-paradox - Carr, M. (2015) ‘Power Plays in Global Internet Governance’, Millennium: Journal of International Studies, 43(2).
Available at: https://journals.sagepub.com/doi/10.1177/0305829814562655 - Haggart, B., Tusikov, N. and Scholte, J. (eds.) (2021) Power and Authority in Internet Governance. Routledge.
Available at: https://www.routledge.com/Power-and-Authority-in-Internet-Governance/Haggart-Tusikov-Scholte/p/book/9780367443930 - Nieborg, D. et al. (2024) ‘Locating and Theorising Platform Power’, Internet Policy Review, 13(2).
Available at: https://policyreview.info/articles/analysis/introduction-special-issue-locating-and-theorising-platform-power
18.5 Appendix E: Media, Government Reports, and Institutional Sources
18.5.1 Government Oversight and Official Reports
- National Audit Office (2016) The Government’s Identity Assurance Programme. London: National Audit Office.
Available at: https://www.nao.org.uk/reports/the-governments-identity-assurance-programme/ - National Audit Office (2023) Digital Government and Identity Services. London: National Audit Office.
Available at: https://www.nao.org.uk/ - UK Cabinet Office (2016) GOV.UK Verify: Identity Assurance Programme.
Available at: https://www.gov.uk/government/publications/identity-assurance-programme - UK Department for Science, Innovation and Technology (2023) Online Safety Act: Policy Statement.
Available at: https://www.gov.uk/government/collections/online-safety-act - Ofcom (2024) Protecting people from illegal harms online.
Available at: https://www.ofcom.org.uk/online-safety - Ofcom (2025) Age assurance and children’s online safety guidance.
Available at: https://www.ofcom.org.uk/online-safety - European Commission (2024) Protecting minors under the Digital Services Act.
Available at: https://digital-strategy.ec.europa.eu
18.5.2 Journalism and Media Coverage
These articles illustrate how the regulatory shift is being covered publicly.
- Financial Times (2024) UK online safety law to force tech platforms to verify users’ ages.
Available at: https://www.ft.com - BBC News (2023) Online Safety Act becomes law in the UK.
Available at: https://www.bbc.com/news/technology - BBC News (2024) How age verification laws could reshape the internet.
Available at: https://www.bbc.com/news/technology - The Guardian (2023) What the UK Online Safety Act means for social media platforms.
Available at: https://www.theguardian.com/technology - The Guardian (2024) Age checks for online content raise privacy concerns.
Available at: https://www.theguardian.com/technology - Reuters (2024) EU Digital Services Act targets social media risks for children.
Available at: https://www.reuters.com/technology - Reuters (2025) Australia enforces social media age restrictions for minors.
Available at: https://www.reuters.com/world/asia-pacific - Politico (2024) Europe moves to regulate algorithms and protect children online.
Available at: https://www.politico.eu - Wired (2023) The global push for age verification online.
Available at: https://www.wired.com - Wired (2024) The fight over age verification and internet privacy.
Available at: https://www.wired.com - The Verge (2023) How new social media laws could force age verification systems.
Available at: https://www.theverge.com - The Verge (2024) Apple and Google face pressure to enforce age checks.
Available at: https://www.theverge.com - Wall Street Journal (2021) The Facebook Files.
Available at: https://www.wsj.com/articles/the-facebook-files-11631713039 - New York Times (2024) Lawmakers worldwide push social media age limits.
Available at: https://www.nytimes.com
18.5.3 Technology Policy Analysis and Think Tank Reports
- Brookings Institution (2023) Regulating Social Media Platforms.
Available at: https://www.brookings.edu - Carnegie Endowment (2023) Platform Governance and Global Regulation.
Available at: https://carnegieendowment.org - Oxford Internet Institute (2024) Platform Regulation and Digital Governance.
Available at: https://www.oii.ox.ac.uk - Center for Democracy & Technology (2024) Age Verification and Privacy Implications.
Available at: https://cdt.org - Electronic Frontier Foundation (2023) The dangers of online age verification.
Available at: https://www.eff.org
18.5.4 Industry and Technical Ecosystem Sources
- Yoti (2024) Age Verification and Age Estimation Technologies.
Available at: https://www.yoti.com - AgeChecked (2023) Age Assurance in Online Services.
Available at: https://www.agechecked.com - Apple (2024) App Store Guidelines and Child Safety Protections.
Available at: https://developer.apple.com/app-store - Google (2024) Play Store Policy on Families and Children.
Available at: https://support.google.com/googleplay
18.6 Appendix F: Optional Suggested Reading
For readers seeking a broader context on the structural issues discussed in this article:
- Lessig, L. (1999) Code and Other Laws of Cyberspace.
- Gillespie, T. (2018) Custodians of the Internet.
- Zuboff, S. (2019) The Age of Surveillance Capitalism.
- Pasquale, F. (2015) The Black Box Society.
- Windley, P. and Reed, D. (2022) Self-Sovereign Identity.
- Haidt, J. (2024) The Anxious Generation.
- Benkler, Y. (2006) The Wealth of Networks.
- Zittrain, J. (2008) The Future of the Internet – And How to Stop It.
18.7 Appendix G: Media Timeline of Age-Verification and Online Safety Regulation (2015–2026)
18.7.1 2015–2017 — First Wave: Pornography Age Verification
The first serious attempts to introduce age verification focused on online pornography rather than social media.
2015
UK Government announces plans to introduce age verification for pornography sites.
BBC News (2015) UK to introduce age checks for online pornography.
https://www.bbc.com/news/technology-34538546
2017
The UK Digital Economy Act introduces mandatory age verification for pornographic websites.
UK Parliament (2017) Digital Economy Act 2017.
https://www.legislation.gov.uk/ukpga/2017/30
The Guardian (2017) UK porn age-verification law explained.
https://www.theguardian.com/technology/2017/apr/11/uk-pornography-age-verification-law
18.7.2 2018–2019 — Collapse of the First Age Verification System
Technical, privacy, and enforcement problems lead to the abandonment of the UK system.
BBC News (2019) UK porn age-verification scheme abandoned.
https://www.bbc.com/news/technology-50073102
Wired (2019) Why the UK’s porn-block experiment failed.
https://www.wired.co.uk/article/uk-porn-block
The debate begins shifting toward platform responsibility instead of individual websites.
18.7.3 2020–2021 — Platform Harm Debate and Whistleblowers
Public attention shifts from pornography to social media harms.
2021
The Facebook Files reveal internal research on youth mental health.
Wall Street Journal (2021) The Facebook Files.
https://www.wsj.com/articles/the-facebook-files-11631713039
BBC News (2021) Facebook whistleblower Frances Haugen testifies to US Congress.
https://www.bbc.com/news/technology-58800191
These disclosures help drive political momentum toward stronger regulation.
18.7.4 2022 — Platform Governance Legislation
Major regulatory frameworks emerge.
European Union adopts the Digital Services Act.
European Commission (2022) Digital Services Act adopted.
https://digital-strategy.ec.europa.eu/en/policies/digital-services-act
Reuters (2022) EU passes sweeping digital platform regulation.
https://www.reuters.com/technology
At the same time, US states begin experimenting with age-verification laws.
Politico (2022) States move to regulate social media for children.
https://www.politico.com
18.7.5 2023 — Online Safety Frameworks
The UK passes the Online Safety Act, a comprehensive regulatory regime for online harms.
UK Parliament (2023) Online Safety Act 2023.
https://www.legislation.gov.uk/ukpga/2023/50
BBC News (2023) Online Safety Act becomes law.
https://www.bbc.com/news/technology-67115653
The Guardian (2023) What the Online Safety Act means for tech companies.
https://www.theguardian.com/technology
Discussion begins focusing on “age assurance” technologies rather than simple verification.
18.7.6 2024 — Youth Social Media Laws
Governments begin targeting social media access by minors.
Australia introduces a national social media age restriction proposal.
Reuters (2024) Australia moves to ban social media for under-16s.
https://www.reuters.com/world/asia-pacific
United States states pass multiple laws regulating youth access.
The Verge (2024) States are forcing social media companies to verify ages.
https://www.theverge.com
Wired (2024) The global push for online age verification.
https://www.wired.com
Policy discussions begin focusing on app stores and operating systems as enforcement layers.
18.7.7 2025 — Enforcement Begins
Major regulatory frameworks begin enforcement phases.
Ofcom launches implementation of the UK Online Safety Act.
Ofcom (2025) Online Safety enforcement programme.
https://www.ofcom.org.uk/online-safety
Financial Times (2025) Tech groups face fines under UK online safety regime.
https://www.ft.com
European Commission begins enforcement of the Digital Services Act risk obligations.
Reuters (2025) EU begins enforcing new tech platform rules.
https://www.reuters.com/technology
18.7.8 2026 — Global Expansion and Infrastructure Debate
By 2026 the policy conversation has shifted toward technical implementation and infrastructure consequences.
BBC News (2026) Age-verification technology becomes central to online safety enforcement.
https://www.bbc.com/news/technology
The Verge (2026) Apple and Google face pressure to implement age-verification signals.
https://www.theverge.com
Wired (2026) The battle over age verification and internet privacy intensifies.
https://www.wired.com
Policy analysts begin discussing whether these systems could lead to identity-mediated internet environments.
